#ITSicherheit #customfirmware #FlipperZero #HackingTool #PentestingTool #RollingCode #Sicherheitslücken https://sc.tarnkappe.info/0e9bfb
#ITSicherheit #customfirmware #FlipperZero #HackingTool #PentestingTool #RollingCode #Sicherheitslücken https://sc.tarnkappe.info/0e9bfb
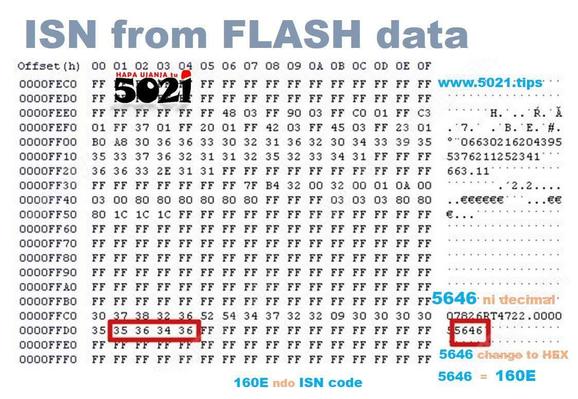
ISN is #rollingcode! It's temporary, a new code generates on every #carkey's #enginestart.
So, this code doesn't mean You forever access the vehicle's #carimmobiliser, seen🤔?
#HapaUjanjaTu, this rubbish makes You #mjanja for #passkeys from #EEPROM's data, do #lostkeys #ECUProgramming #ecurepair👇
https://www.5021.tips/ujanja/keyprogramming
👆☝️
#InshaAllah, may whatever nonsense make sense do #carkeyprogramming #smartkeyprogramming #immoff #programmingtips #5021tips #techtips #autoelectronics
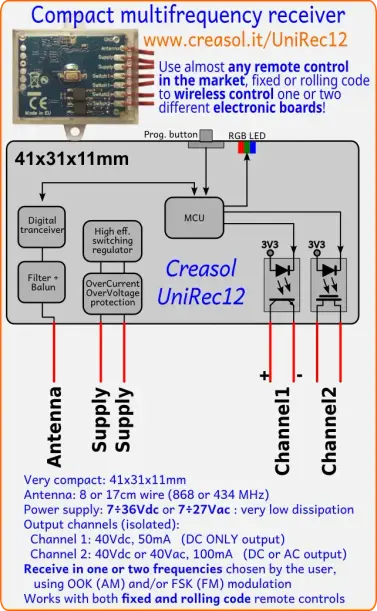
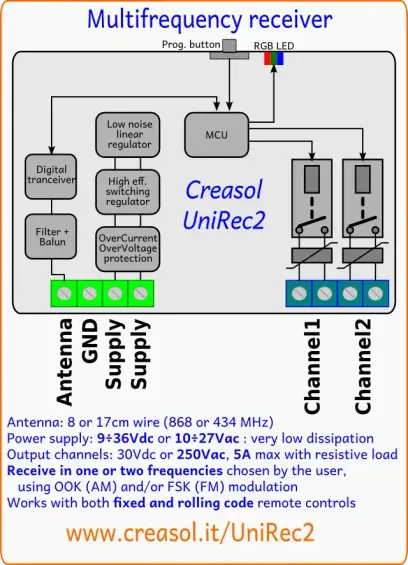
Permits to control one or two electronic boards by #wireless #remotecontrol #transmitters 433.92 MHz 868.3 MHz and other frequencies. store.creasol.it/UniRec12
@Laberpferd @DO9XE Muss mal nachlesen auf der Seite der @BNetzA ...
- Soweit ich weiß ist #CB sowieso "Tertiärnutzer" im 27MHz-Band und ne Menge #Funkfernsteuerungen nutzen (wenn auch kryptographisch schwache) #RollingCode / #Fibonacci-basierte #Verschlüsselungen, wobei im #ISM-Band dann ja auch harte "Sendedauer" - Grenzen gibt...
Wobei im Zweifelsfalle #AX25 auf CB mit verschlüsselten Datenpaketen die Forderung nach "Offenem Standard" erfüllen sollte.
#carhacks #securityhacks #honda #keyfob #replayattack #rollingcode #sdr #hackaday
posted by pod_feeder_v2
Unlock Any (Honda) Car (https://hackaday.com/2022/07/08/turns-out-y...
Unlock Any (Honda) Car (https://hackaday.com/2022/07/08/turns-out-you-can-just-unlock-any-honda-car/) image https://hackaday.com/wp-content/uploads/2022/07/hadimg_honda_rollingpwn_feat.png #carhacks #securityhacks #honda #keyfob #replayattack #rollingcode #sdr #hackaday posted by pod_feeder_v2 (https://gitlab.com/brianodonnell/pod_feeder_v2/)
Hacker Claims Honda and Acura Vehicles Vulnerable to Simple Replay Attack
Keyless entry has become a standard feature on virtually all cars, where once it was a luxury option. However, it's also changed the way that thieves approach the process of breaking into a car. After recent research, [HackingIntoYourHeart] claims that many modern Honda and Acura vehicles can be accessed with a simple replay attack using cheap hardware.
It's a bold claim, and one that we'd love to see confirmed by a third party. The crux of the allegations are that simply recording signals from a Honda or Acura keyfob is enough to compromise the vehicle. Reportedly, no rolling code system is implemented and commands can easily be replayed.
Given these commands control features like unlocking the doors, opening the trunk, and even remote starting the vehicle, it's a concerning situation. However, it's also somewhat surprising. Rolling code technology has been around for decades, and makes basic replay attacks more difficult. Range extender attacks that target keyfobs sitting inside homes or gas stations are more common these days.
Whether Honda has made a security faux pas, or if there's something more at play here, remains to be seen. If you've got more information, or have been able to recreate the same hack on your own Honda, be sure to let us know.