La cybersécuritay, c'est compliquay. Comment la Corée du Nord a coupé sa liaison Internet en voulant la sécuriser. https://labs.ripe.net/author/romain_fontugne/from-bgp-data-to-insight-simplifying-real-time-routing-analysis/
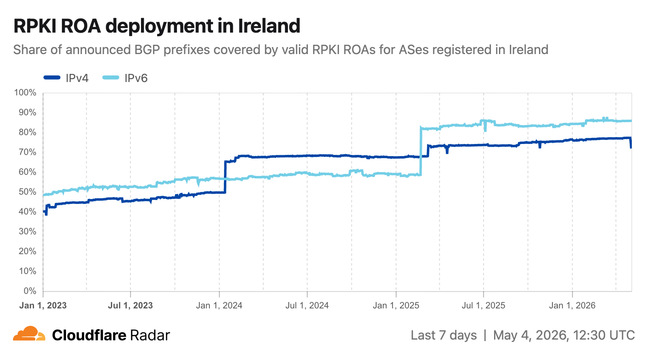
🚨 More new routing insights on Radar!
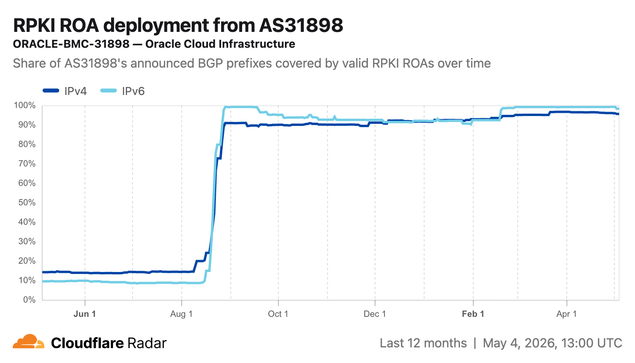
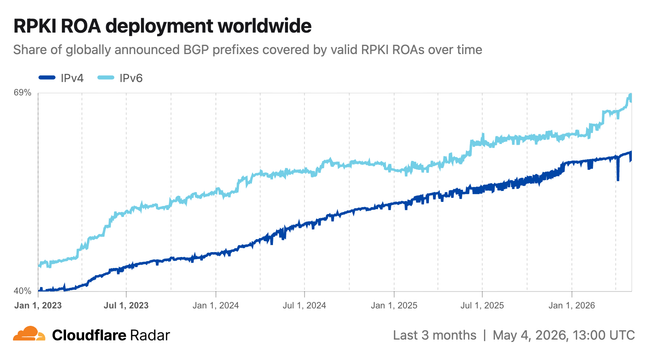
- Track #RPKI ROA deployment history at a global/country/ASN level, going back 3+ years for valid prefixes & address space
https://radar.cloudflare.com/routing/rpki#rpki-roa-deployment
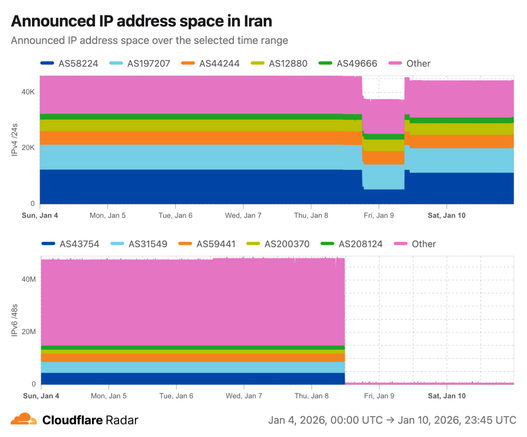
- Country level announced IP address space graphs now include a "Show top ASes" toggle. Stacked area graphs make it easier to identify the providers behind large address space withdrawals.
Weekend Reads
* How crazy is .internal/DOT
https://ant.isi.edu/~hardaker/papers/2026-04-27-analyzing-dot-internal-to-dot.pdf
* RIPE NCC RPKI exploit chain
https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
* Bellovin book: Don't get hacked
https://www.cs.columbia.edu/~smb/homesec/index.html
* Internet Protocol Journal May 2026
https://ipj.dreamhosters.com/wp-content/uploads/2026/04/291-ipj.pdf
* Cloudflare 2026-Q1 Internet disruptions report
https://blog.cloudflare.com/q1-2026-internet-disruption-summary/
As the RPKI ecosystem continues to evolve to provide the data for securing BGP Internet routing, the foundations are being laid for the long term need for forensic analysis tools and the long term study of that ecosystem.
For BGP, we've long had the MRT files gathered by various looking glass projects such as route-views. That data today is part of long term trend analysis for BGP and a tool for triaging global routing problems.
The rpki-views work and related IETF drafts for it, largely driven by Job Snijders, is providing a way to capture the state of the RPKI. As Internet routing analysis eventually becomes more dependent on the state of the RPKI at a given moment, such state becomes a critical component of any ex post facto analysis of BGP routing security from BGP routing data.
While the attached article is effectively discussing an "oops" while building out this ecosystem, it provides a good set of links to spelunk for the above topics.
https://blog.qrator.net/en/repairing-the-rpkiviews-h1-2026-archives_227/
rpki-client 9.8 released
Routing security matters to all of us (even those of us who seldom give the subject any thought), and the rpki-client project announced the release of a new version of their Resource Public Key Infrastructure (RPKI) client, with a number of improvements.
The announcement reads
- List: openbsd-announce
- Subject: rpki-client 9.8 released
- From: Sebastian Benoit
Date: 2026-04-14 23:20:42
rpki-client 9.8 has just been released and will be available in the rpki-client directory of any OpenBSD mirror soon.
It is recommended
that all users upgrade to this version for improved reliability.rpki-client is a FREE, easy-to-use implementation of the Resource
Public Key Infrastructure (RPKI) for Relying Parties to facilitate
validation of BGP announcements. The program queries the global RPKI
repository system and validates untrusted network inputs. The program
outputs validated ROA payloads, BGPsec Router keys, and ASPA payloads
in configuration formats suitable for OpenBGPD and BIRD, and supports
emitting CSV and JSON for consumption by other routing stacks.See RFC 6480 and RFC 6811 for a description of how RPKI and BGP Prefix
Origin Validation help secure the global Internet routing system.rpki-client was primarily developed by Kristaps Dzonsons, Claudio Jeker,
Job Snijders, Theo Buehler, Theo de Raadt, and Sebastian Benoit as part
of the OpenBSD Project.This release includes the following changes to the previous release:
- Various refactoring for improved compatibility with various libcryptoimplementations and in CA/BGPsec certificate handling.
- Fixed an accounting issue in HTTP gzip compression detection.
- Added a warning in extra verbose mode (-vv) about standardsnon-compliant Issuer and Subject ASN.1 string encodings.
- Added a check for canonical encoding of ASPA eContent in alignmentwith draft-ietf-sidrops-aspa-profile-22.
- Ensure that a repository timeout correctly stops repositoryprocessing. Thanks to Fedor Vompe from Deutsche Telekom for reporting.
- Fixed a defect in Canonical Cache Representation ROAIPAddressFamilysort order. As a result, rpki-client 9.8 cannot parse rpki-client9.7's .ccr files and vice versa. Thanks to Bart Bakker from RIPE NCCfor reporting.
- Fixed an issue in the parser for the locally configured constraints.Thanks to Daniel Anderson.
- A malicious RRDP Publication Server can cause a NULL dereference.Thanks to Daniel Anderson for reporting.
- A malicious RPKI Publication Server can cause an incorrect error exit.Thanks to Yuheng Zhang, Qi Wang, Jianjun Chen from Tsinghua University,and Teatime Lab for reporting.
Go read ALL about it here!
https://undeadly.org/cgi?action=article;sid=20260415115612
#rpki #client #resource #public #key #infrastructure #openBSD #OpenSource #programming #networking
https://github.com/macports/macports-ports/pull/32251
GitHub Continuous Integration checks passed OK!
It's up to someone else to merge it.
I couldn't help but notice the most recent OpenBGPD release announcement mentioned something about a -portable branch? Admittedly, it has been a very long time since I looked at building OpenBGPD on macOS, but maybe it is worth looking at again? I still think it is probably ill advised to use macOS for something as critical as routing insomuch as it sleeps, with abandon, unless /usr/bin/caffeinate is invoked.
#RPKI #MacPorts #rpkiーclient #RPKIclient #OpenSource #BGP #Routing
On Tuesday, 7 April, the Global Internet Standards Testing Community (GISTC) held its 3rd online meeting, which was chaired by Alena Muravska from @ripencc.
The GISTC brings together organisations from all over the world around #InternetStandards the Internet.nl test tool and open-source code.
Its goal is to enable knowledge exchange, coordination of efforts, and of course to collaboratively improve the adoption of modern internet standards like #IPv6, #DNSSEC, #DANE, #DMARC, and #RPKI.
1/3
Weekend Reads
* Email address obfuscation in 2026
https://spencermortensen.com/articles/email-obfuscation/
* Profile of Kimwolf botnet researcher
https://www.wsj.com/tech/kimwolf-hack-residential-proxy-networks-a712ab59?st=dHJ5oe
* Quantifying AI data center heat impacts
https://arxiv.org/abs/2603.20897
* Characterizing invalid routes via Tunnels
https://arxiv.org/abs/2603.29207
* Detecting anomalous topology, routes, and congestion
https://arxiv.org/abs/2603.25875
➤ 透過 RPKI 認證機制,築起網際網路路由的安全防線
✤ https://isbgpsafeyet.com/
邊界閘道協定(BGP)作為網際網路的「郵政系統」,負責為數據選定最佳路徑,然而其先天設計缺乏安全性,導致全球網路經常面臨幹擾風險。Cloudflare 指出,唯有透過名為 RPKI 的認證體系,纔能有效防堵惡意路由注入。近年來,隨著全球各大電信商與網際網路服務供應商(ISP)如 Verizon、Comcast 與 Sparkle 等陸續加入防護行列,採用 RPKI 源位址驗證(Origin Validation)並過濾無效路由,網際網路的安全基石正在逐步強化。
+ 網路底層架構的演進總是異常緩慢,看到這麼多大型營運商終於開始過濾無效路徑,總算讓人對網際網路的可靠性稍微放心了一些。
+ RPKI 固然重要,但這終究是一個去中心化的挑戰,如果還有大型 ISP 不跟進,整個路由體系的脆弱點依然存在。
#網路安全 #路由安全 #BGP #RPKI

Is BGP safe yet? · Cloudflare
On the Internet, network devices exchange routes via a protocol called BGP (Border Gateway Protocol). Unfortunately, issues with BGP have led to malicious actors being able to hijack and misconfigure devices leading to security problems which have the potential to cause widespread problems. BGP security can be greatly improved by using technologies such as RPKI to sign Internet routes. This page attempts to track the progress of major Internet players (ISPs, transit operators, and content providers) in their progress to adopt RPKI and other technologies.