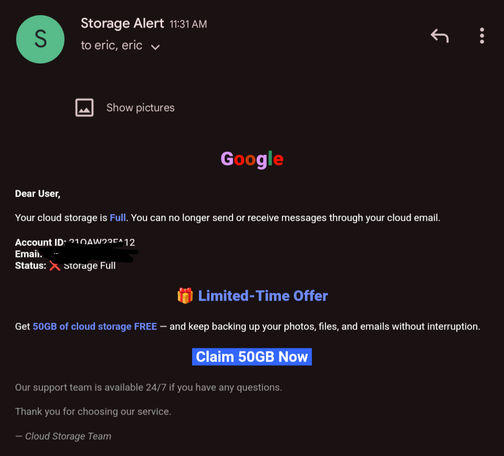
🚨 ALERT: #Phishers use fake online shops with surveys to steal users’ credit card information
⚠️ The new phishing scheme we named #FoxWhoops targets American customers of the e-commerce with fake sites promising a reward for completing a survey
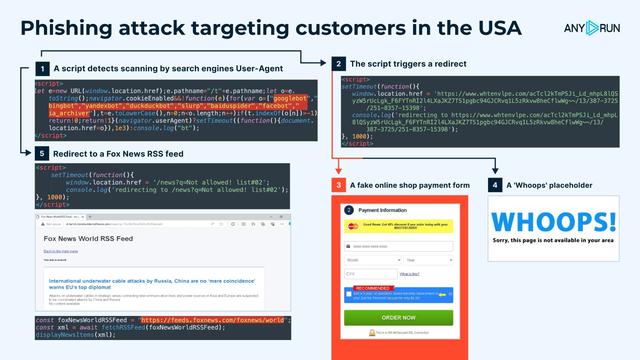
📌 The attack utilizes a system of checks, sending users who fail them to a Fox News RSS page or a page with a ‘Whoops!’ image. Those who pass the checks are offered to enter their bank card info to purchase the ‘reward’ at a discount
Examples:
Fake Market: https://app.any.run/browses/566dac16-0dee-4343-9dc7-ad9e6c71a780/?utm_source=mastodon&utm_medium=post&utm_campaign=foxwhopps&utm_term=160125&utm_content=linktoservice
FoxNews RSS: https://app.any.run/tasks/e5bab257-0de4-4ef9-801e-756b88598649/?utm_source=mastodon&utm_medium=post&utm_campaign=foxwhopps&utm_term=160125&utm_content=linktoservice
Whoops!: https://app.any.run/tasks/28b68210-807f-4beb-bd6c-720fc0c61f8f/?utm_source=mastodon&utm_medium=post&utm_campaign=foxwhopps&utm_term=160125&utm_content=linktoservice
🔗 Checks and redirects:
1. A script that detects scanning by Google, Bing, Baidu, DuckDuck, etc.
2. If the first check is passed, the script triggers a redirect
3. If the second check is passed, the user is redirected to a #phishing page with a fake online shop payment form
4. If the second check fails, the ‘Whoops’ page is displayed
5. If the first check fails, the user is redirected to a Fox News RSS feed
Here are three scenarios showing how a user’s browser might navigate through this phishing campaign:
1️⃣ 𝗣𝗵𝗶𝘀𝗵𝗶𝗻𝗴 𝘀𝗰𝗲𝗻𝗮𝗿𝗶𝗼 (𝟭 → 𝟮 → 𝟯) Credit card info theft. A phishing survey with a ‘reward’ after a small payment in a fake store
2️⃣ 𝗘𝘃𝗮𝘀𝗶𝗼𝗻 𝘀𝗰𝗲𝗻𝗮𝗿𝗶𝗼 (𝟭 → 𝟱) If the victim fails the first check, they are redirected to what appears to be a Fox News RSS feed. The URL includes a ‘q’ parameter that specifies the reason for the redirect, such as:
IP provider is blacklisted! ASN-CXA-ALL-CCI-22773-RDC
3️⃣ 𝗣𝗹𝗮𝗰𝗲𝗵𝗼𝗹𝗱𝗲𝗿 𝘀𝗰𝗲𝗻𝗮𝗿𝗶𝗼 (𝟭 → 𝟮 → 𝟰) Users are shown a placeholder page
🎯 Use this #TI Lookup query to gather info on this campaign:
https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=foxwhoops&utm_content=linktoti&utm_term=160125#%7B%2522query%2522:%2522url:%255C%2522/news?q=%255C%2522%2520and%2520threatName:%255C%2522phishing%255C%2522%2520%2522,%2522dateRange%2522:180%7D
Or find sandbox sessions with the ‘whoops’ tag and gather #IOCs:
https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=foxwhoops&utm_content=linktoti&utm_term=160125#%7B%2522query%2522:%2522threatName:%255C%2522foxwhoops%255C%2522%2522,%2522dateRange%2522:180%7D
Analyze and investigate the latest #malware and phishing threats with ANYRUN 🚀
#cybersecurity #infosec