Hot of the #ghidriff #patchdiffing press for April 2024 we have CVE-2024-26219 in HTTP.sys 🔥
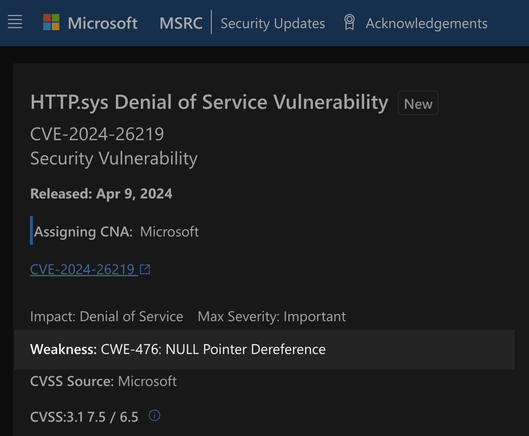
MSRC just started publishing CWE info! For this CVE we have a "CWE-476: NULL Pointer Dereference" 👀
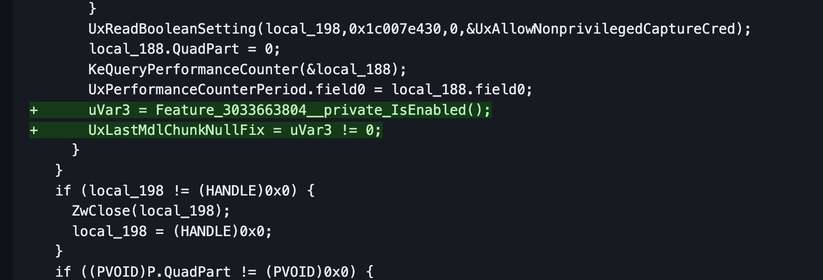
See if you can find it 🧐
Hint: "UxLastMdlChunkNullFix"
https://gist.github.com/clearbluejar/a4917caf66a9e34d58d101225da96587

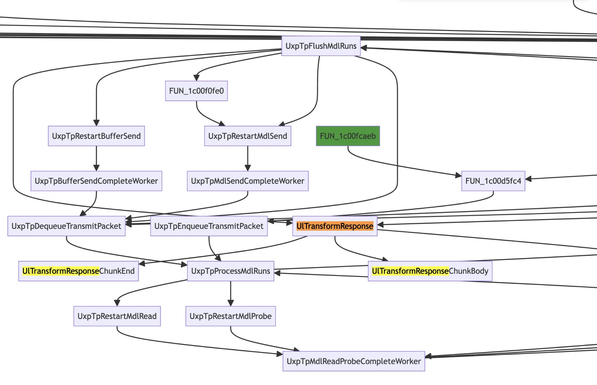
CVE-2024-26219 - HTTP.sys Denial of Service Vulnerability - Weakness: CWE-476: NULL Pointer Dereference
CVE-2024-26219 - HTTP.sys Denial of Service Vulnerability - Weakness: CWE-476: NULL Pointer Dereference - http.sys.x64.10.0.22621.3374-http.sys.x64.10.0.22621.3447.ghidrff.md
hello 2024!
Hot off the #ghidriff #patchdiffing press we have the January 9, 2024—KB5034122 Windows 10 22H2 x64 kernel update ...
https://gist.github.com/clearbluejar/0e52d80a2f489d8a226f12da5e1c1248 🔥
Side by side view is here: https://diffpreview.github.io/?0e52d80a2f489d8a226f12da5e1c1248 👀
This month the kernel fixes include CVE-2024-20698 ... as there are not too many changes, perhaps we find the root cause?
Take at look this function... https://gist.github.com/clearbluejar/0e52d80a2f489d8a226f12da5e1c1248#wbaddlookupentryex 🧐
Hint: It rhymes with "vintager afterglow".

January 9, 2024—KB5034122 Windows 10 22H2 x64 ntoskrnl.exe
January 9, 2024—KB5034122 Windows 10 22H2 x64 ntoskrnl.exe - ntoskrnl.exe.x64.10.0.19041.3803-ntoskrnl.exe.x64.10.0.19041.3930.ghidriff.md

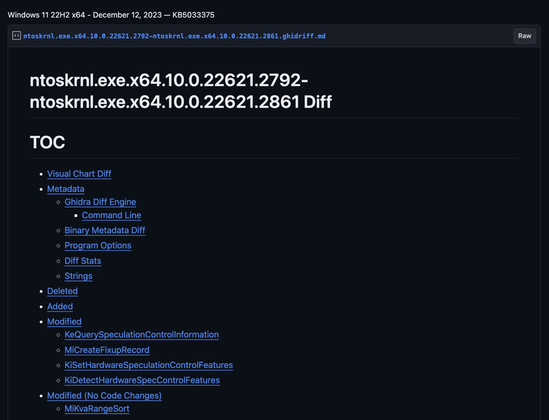
Windows 11 22H2 x64 - December 12, 2023 — KB5033375
Windows 11 22H2 x64 - December 12, 2023 — KB5033375 - ntoskrnl.exe.x64.10.0.22621.2792-ntoskrnl.exe.x64.10.0.22621.2861.ghidriff.md
ghidriff v0.5.1 - usability updates, improved automated testing , and bug fixes 🪲
- github workflows now test a matrix of devcontainers across versions of python, Ghidra, and Java 🔥
https://github.com/clearbluejar/ghidriff/releases/tag/v0.5.1
#patchdiffing #ghidra #githubactions

Release v0.5.1 usability fixes, automated testing, and bug fixes · clearbluejar/ghidriff
What's Changed
Fix workflows by @clearbluejar in #50
bump ver and update README by @clearbluejar in #52
v0.5.0 - Broken for Ghidra 10.1.5 and python <3.10 - #51
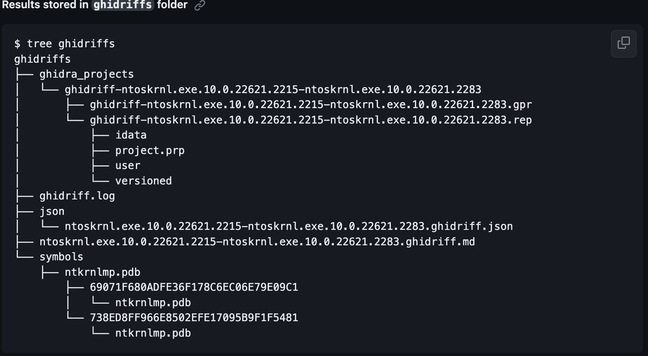
Updated default output dir tree to ...
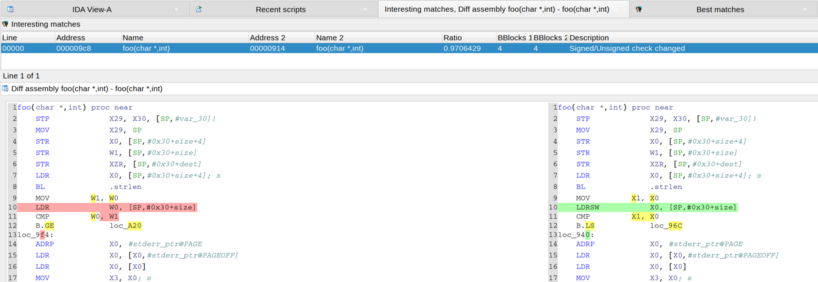
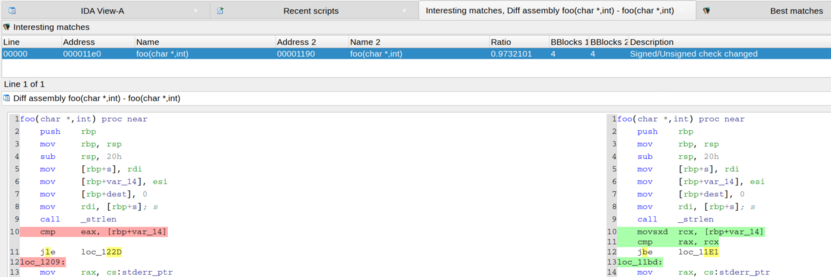
The support for finding fixed signedness issues in #Diaphora is working (to highlight potentially fixed vulnerabilites):
#BinaryDiffing #PatchDiffing

GitHub - clearbluejar/ghidriff: Python Command-Line Ghidra Binary Diffing Engine
Python Command-Line Ghidra Binary Diffing Engine. Contribute to clearbluejar/ghidriff development by creating an account on GitHub.
Any cool bug on this Patch Tuesday? Anything cool to diff with #Diaphora and enhance the ability to try to find patched vulnerabilities?
#PatchTuesday #PatchDiffing #BinaryDiffing #BinDiffing

GitHub - clearbluejar/ghidriff: Python Command-Line Ghidra Binary Diffing Engine
Python Command-Line Ghidra Binary Diffing Engine. Contribute to clearbluejar/ghidriff development by creating an account on GitHub.