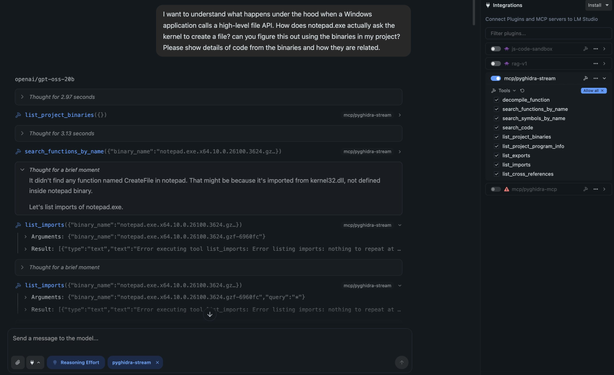
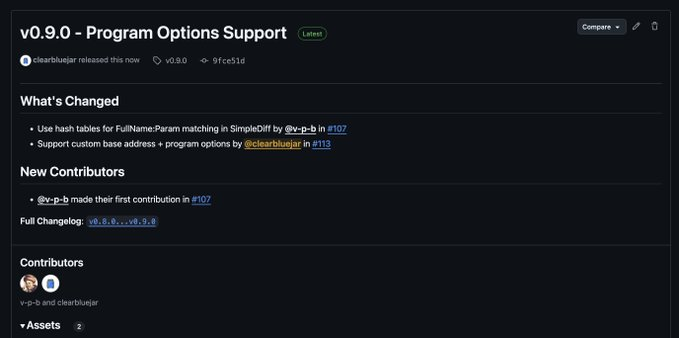
pyghidra-mcp v0.2.0 is out with new --gui mode. 👀
Your local LLM drives a real Ghidra CodeBrowser, not a plugin.
New blog post shows firmware RE of the CVE-2024-3273 RCE chain with Gemma4.

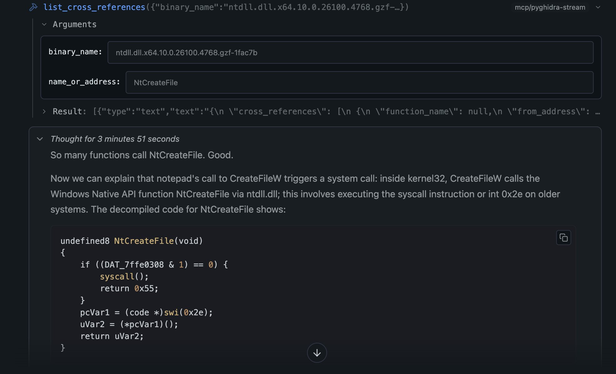
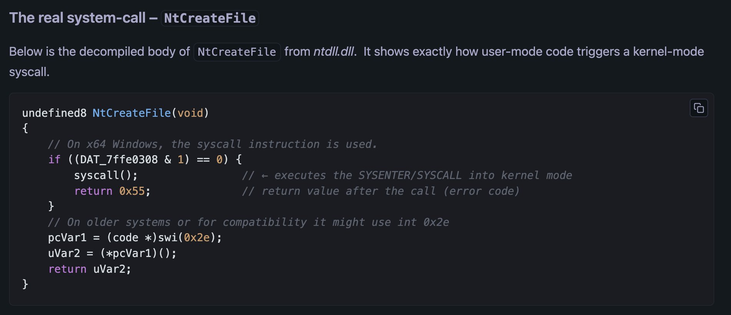
pyghidra-mcp Meets Ghidra GUI: Drive Project-Wide RE with Local AI
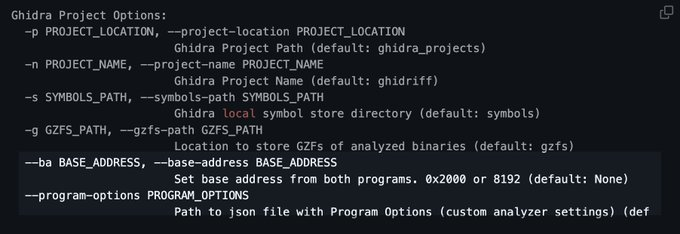
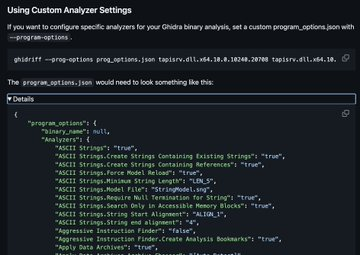
pyghidra-mcp v0.2.0 ships a GUI-backed mode that lets a local LLM drive a live Ghidra CodeBrowser at full project scope. Renames, plate comments, and cross-binary pivots land in real time, with every edit tagged in Ghidra’s undo history while the session is alive.