⚡ Fresh Talk Alert for BSides Luxembourg 2026!
𝗬𝗢𝗨𝗥 𝗖𝗧𝗜 𝗥𝗘𝗣𝗢𝗥𝗧𝗦 𝗔𝗥𝗘 𝗨𝗦𝗘𝗟𝗘𝗦𝗦 𝗪𝗜𝗧𝗛𝗢𝗨𝗧 𝗦𝗧𝗥𝗨𝗖𝗧𝗨𝗥𝗘: 𝗙𝗥𝗢𝗠 𝗨𝗡𝗦𝗧𝗥𝗨𝗖𝗧𝗨𝗥𝗘𝗗 𝗧𝗛𝗥𝗘𝗔𝗧 𝗜𝗡𝗧𝗘𝗟 𝗧𝗢 𝗦𝗧𝗜𝗫 𝗞𝗡𝗢𝗪𝗟𝗘𝗗𝗚𝗘 𝗚𝗥𝗔𝗣𝗛𝗦 𝗪𝗜𝗧𝗛 𝗟𝗟𝗠𝗦 𝗔𝗡𝗗 𝗠𝗖𝗣 𝗦𝗘𝗥𝗩𝗘𝗥 – Antonio Formato
Turn unstructured threat intelligence into actionable, machine-readable defense logic in this deep dive from the Actionable CTI & Detection Engineering Village. Every week, critical threat reports are published in PDFs and blog posts — rich in insight but unusable for SIEMs, SOARs, or AI agents. This talk shows how to bridge that gap using a hybrid architecture that combines deterministic extraction and LLM-based semantic inference to generate STIX 2.1 knowledge graphs.
You’ll explore how threat reports can be transformed into structured intelligence objects, mapped to MITRE ATT&CK, and visualized as interactive knowledge graphs. The session also introduces TI Mindmap HUB, an independent research platform that converts real-world reports into multi-layered CTI views including ATT&CK heatmaps, Diamond Model structures, and CVE prioritization.
A key focus is the Model Context Protocol (MCP), which exposes structured CTI as tool calls for AI agents—making intelligence directly usable in automated workflows, SOC tooling, and AI copilots. The talk concludes with emerging research into LLM-inferred threat intelligence knowledge graphs and cross-report correlation at scale.
Antonio Formato is a Senior Cybersecurity Solution Engineer at Microsoft and an independent researcher focused on Generative AI for Cyber Threat Intelligence. He is the creator of TI Mindmap HUB and co-author of academic research on automated STIX 2.1 generation currently under peer review.
📅 Conference Dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule: https://hackertracker.app/schedule?conf=BSIDESLUX2026
#BSidesLuxembourg2026 #CTI #ThreatIntelligence #STIX #MITREATTACK #AISecurity #DetectionEngineering
🎮 The Return of Malware & Monsters: Collaborative IR Gaming (2h Workshop) on May 6th!
𝗚𝗢𝗧𝗧𝗔 𝗖𝗢𝗡𝗧𝗔𝗜𝗡 '𝗘𝗠 𝗔𝗟𝗟: 𝗖𝗢𝗟𝗟𝗔𝗕𝗢𝗥𝗔𝗧𝗜𝗩𝗘 𝗜𝗡𝗖𝗜𝗗𝗘𝗡𝗧 𝗥𝗘𝗦𝗣𝗢𝗡𝗦𝗘 𝗧𝗥𝗔𝗜𝗡𝗜𝗡𝗚 𝗧𝗛𝗥𝗢𝗨𝗚𝗛 𝗚𝗔𝗠𝗜𝗡𝗚 with Klaus Agnoletti (@klausagnoletti) & 𝗚𝗟𝗘𝗡 𝗦𝗢𝗥𝗘𝗡𝗦𝗘𝗡 - 6 May, 9AM - 11AM
Back by popular demand after last year's hit! Ditch dull tabletops for Malware & Monsters – tabletop RPG meets creature-collecting where teams hunt/contain digital threats in story-driven scenarios with MITRE ATT&CK-mapped malware "malmons." Experience real IR chaos: coordination under pressure, incomplete intel, stakeholder drama. Take roles like Hunter, Analyst, Forensicator, Communicator to see how teams actually collaborate. Learn mechanics, build custom scenarios from real malware history, run live sims with "type effectiveness" for defenses and evolution for escalating attacks. Walk away with free, ready-to-use materials for fun, effective IR training.
Led by Klaus Agnoletti https://pretalx.com/orga/event/bsidesluxembourg-2026/speakers/SQVVHK/ (infosec pro since 2004, BSides København co-founder, storytelling cyber advisor, neurodiversity advocate) & Glen Sorensen https://pretalx.com/orga/event/bsidesluxembourg-2026/speakers/J3PRCC/ (Recovering CISO, DeleteMe Solutions Engineer, OSINT/AI expert, HackBack Gaming Incident Master).
📅 Conference dates and time: 6–8 May 2026 | 9AM - 6PM
📍 Venue: 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule: https://pretalx.com/bsidesluxembourg-2026/schedule/
Game your way to better IR skills – popular return engagement! 🎲
#BSidesLuxembourg2026 #IncidentResponse #CyberSecurityTraining #BlueTeam #GameBasedLearning #MITREATTACK #BSides #DnD #DFIR
If the Kardashians launched their own framework it would be Kommand and Kontrol (K2).
The Momager (Kris.exe or Kris.sh): The primary C2 listener.
The Glow Up: Privesc
Keeping Up: Lateral movement
#C2Framework #RedTeaming #PostExploitation #MalwareDevelopment #Infosec #CyberSecurity #EDRBypass #ActiveDirectory #PenTesting #ThreatHunting #MITREATTACK #APTHunting #Shellcode #ZeroDay #Persistence #Exfiltration #BlueTeam #PurpleTeaming #kardashians
Why the MITRE ATT&CK Framework Actually Works: https://levelup.gitconnected.com/why-the-mitre-att-ck-framework-actually-works-29ac26d2d20c
Learn How Malware Survives Reboots and Cleanup Using Cron Persistence Technique in Linux Systems.
Full Details Here: https://ostechnix.com/cron-persistence-linux-malware/
#CronPersistence #Malware #Cronjob #Cron #LinuxSecurity #MitreAttack #Linux
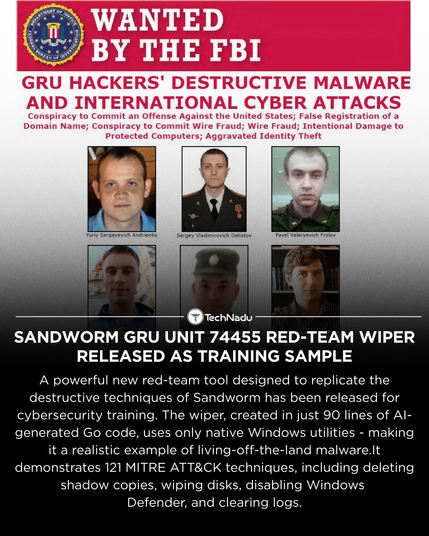
A red-team wiper emulating Sandworm (GRU Unit 74455) has been published - a 90-line Go binary demonstrating LotL execution across 121 MITRE ATT&CK techniques including T1490, T1561.001, and T1070.001.
Full report:
https://www.technadu.com/sandworm-gru-unit-74455-red-team-wiper-released-as-training-sample/614498/
Follow @technadu for more threat intel updates.
#Sandworm #GRU74455 #MITREATTACK #RedTeam #BlueTeam #Infosec #WiperMalware
Red and blue teams breaking down their silos and working in real time—imagine a cybersecurity defense that evolves with every simulated threat. Curious how continuous purple teaming is rewriting the playbook?
#purpleteaming
#cyberdefense
#breachandattacksimulation
#mitreattack
#redteam
#blueteam
#securityautomation
#continuousvalidation
#cybersecuritystrategy
🚀 MITRE ATT&CK v18 = a major leap in detection depth.
The new version adds Detection Strategies and Analytics - helping defenders align detection logic to platform-specific threats.
Also new: CI/CD, Kubernetes, ransomware prep behaviors, mobile “linked devices” exploits, and ICS asset updates.
MITRE even launched the ATT&CK Advisory Council to strengthen community collaboration.
💬 What part of ATT&CK v18 do you think will have the biggest impact on detection engineering?
Follow @technadu for more #ThreatIntel insights.
#CyberSecurity #MITREATTACK #DetectionEngineering #CTI #ThreatIntel #BlueTeam #Infosec #CyberDefense #MITRE #ICS #CloudSecurity #MobileSecurity
New phishing technique - CoPhish - weaponizes Microsoft Copilot Studio to steal Entra ID OAuth tokens.
Attackers build malicious AI agents hosted on legitimate Microsoft domains, exfiltrating tokens via “Login” flows that appear genuine.
Uses OAuth T1528 techniques + token forwarding through Microsoft IPs for stealth.
🛡️ Detection ideas:
- Monitor consent grants in Entra ID logs.
- Restrict unverified app registrations.
- Disable user app creation.
- Flag Copilot bots using trial tenants or untrusted domains.
How are you tuning detections for AI-driven OAuth phishing?
💬 Share your strategies & follow @technadu for more technical threat intel.
#OAuth #Phishing #Microsoft #Copilot #CloudSecurity #ThreatHunting #AIsecurity #EntraID #MITREATtack #InfoSec #TechNadu