I found a budget bypass in #LiteLLM, since they don't pay here you go https://github.com/LargeHardonCollider/litellm-infinite-money-glitch
CVE Alert: CVE-2026-42208 - BerriAI - litellm - https://www.redpacketsecurity.com/cve-alert-cve-2026-42208-berriai-litellm/
#OSINT #ThreatIntel #CyberSecurity #cve-2026-42208 #berriai #litellm
Data Breaches Surge, Exposing Sensitive Info at AI Startups, Agencies
Data breaches are surging, with AI startups and agencies exposed, as seen in the alarming theft of 10 petabytes from a Chinese supercomputer and 4 terabytes from AI startup Mercor due to a supply-chain vulnerability. These incidents highlight the hidden risks of connecting data to AI models, creating sensitive blind spots that leave large…
Embeddings models from #Scaleway weren't working with #LiteLLM. Couple of hours of searching and testing, it's a three line fix. 😅
fix(embedding): omit null encoding_format for openai requests by meutsabdahal · Pull Request #25395 · BerriAI/litellm
Relevant issues Fixes #25388 Pre-Submission checklist Please complete all items before asking a LiteLLM maintainer to review your PR I have Added testing in the tests/test_litellm/ directory, Add...
https://securityaffairs.com/191483/hacking/cve-2026-42208-litellm-bug-exploited-36-hours-after-its-disclosure.html
#securityaffairs #hacking
🔐 LiteLLM sotto assedio: scoperta falla che mette a rischio le chiavi IA. Tempo di rinforzare la sicurezza! #LiteLLM #CyberSecurity
🔗 https://www.tomshw.it/hardware/litellm-sotto-attacco-falla-espone-chiavi-ia
LiteLLM SQL Flaw Exploited 36 Hours After Disclosure
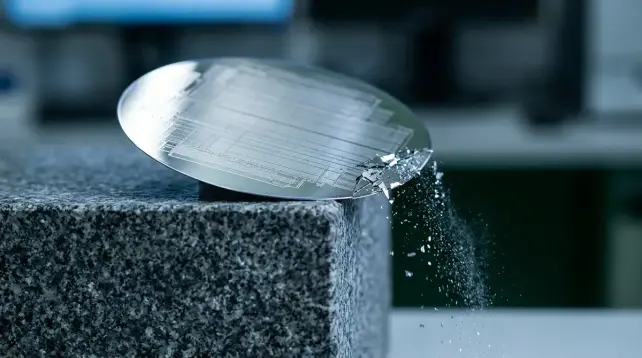
A critical SQL injection flaw, CVE-2026-42208, was exploited just 36 hours after its disclosure, putting vulnerable LiteLLM versions at risk of unauthorized database access. The bug, with a CVSS score of 9.3, allows unauthenticated callers to reach a vulnerable database query through the proxy's error-handling path.
#SqlInjection #Litellm #Cve202642208 #Python #EmergingThreats
Urgent security alert: Hackers are exploiting a pre-authentication SQL injection flaw (CVE-2026-42208) in LiteLLM, allowing them to bypass authentication and exfiltrate sensitive AI provider credentials. Sysdig Threat Research Team observed attackers moving directly to high-value tables, demonstrating precise knowledge. This vulnerability's impact is comparable to a full cloud-account…
#cybersecurity #litellm #cve202642208
🤖 This post was AI-generated.