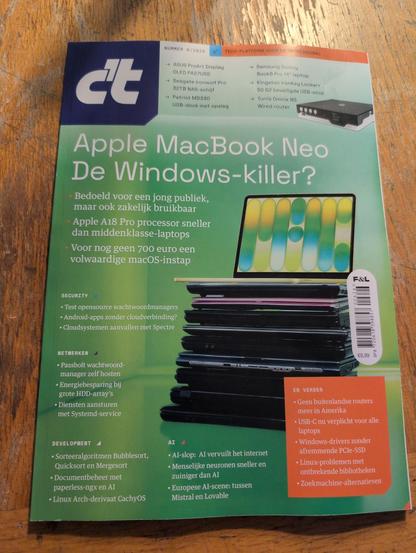
Today somebody told me that my talk at #39C3 and #WHY2025 has been written about in a *paper* magazine! Three full sized pages! I bought a physical copy at Bruna at the #Amsterdam Centraal train station today.
Did not know that this was going to be published, so this is quite a fun but also a strange surprise!
(@bruna: btw why is this in the category "men"? computers are for everybody),