🔴 NEW: Kubernetes Misconfigs Hackers Exploit in 2024
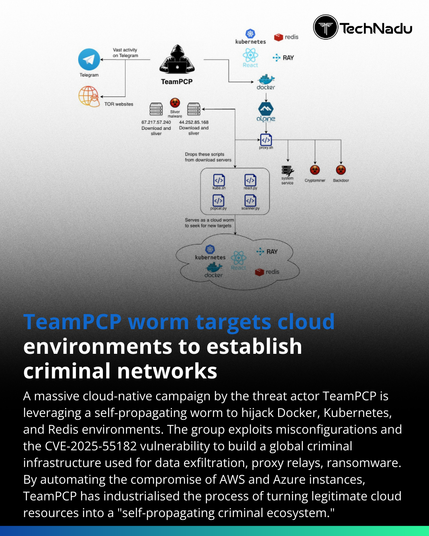
Hackers exploit Kubernetes misconfigs daily - no zero-days needed. We cover the top 3: anonymous auth, overprivileged RBAC, and privileged containers. Real CVEs, real breaches, real fixes. Run kube-be
https://www.youtube.com/watch?v=Fj5s2g1pub8
#KubernetesSecurity #CloudSecurity #DevSecOps #ContainerSecurity #Cybersecurity2024 #Kubernetesmisconfigurationsecurity #KubernetesRBACexploit #kubernetesanonymousauthvulnerability