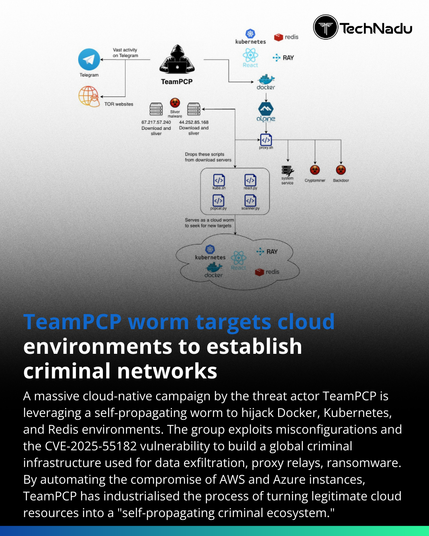
The TeamPCP campaign highlights how cloud-native misconfigurations can be industrialized into a full cybercrime platform.
By abusing exposed Docker APIs, Kubernetes clusters, Redis, and vulnerable web apps, the group automates scanning, persistence, proxying, data theft, and monetization - often without novel exploits. This reinforces that operational scale, not exploit sophistication, is now the primary threat driver in cloud environments.
Source: https://thehackernews.com/2026/02/teampcp-worm-exploits-cloud.html
💬 Are cloud control planes receiving enough defensive visibility?
🔔 Follow @technadu for ongoing cloud threat analysis
#InfoSec #CloudSecurity #KubernetesSecurity #ThreatResearch #MalwareOps #CyberCrime #TechNadu