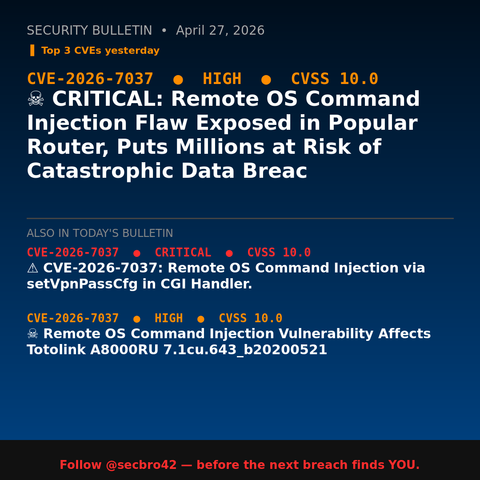
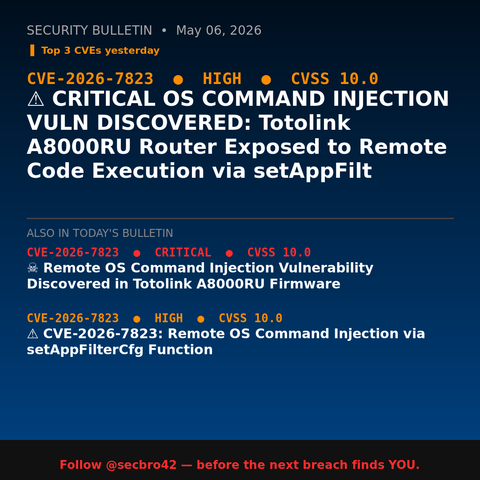
Wordfence: vulnerabilidades críticas WordPress mayo 2026
¿Tus plugins están en la lista? El reporte vulnerabilidades WordPress Wordfence de esta semana incluye Eventin con 70k sitios afectados y backdoors acti...
https://seguridadenwordpress.com/reporte-vulnerabilidades-wordpress-wordfence-abril-mayo-2026/
#wordfence #vulnerabilidadeswordpress #cve2026 #supplychain #pluginswordpress



 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉