The Register: 60% of MD5 password hashes are crackable in under an hour. “Using a dataset of more than 231 million unique passwords sourced from dark web leaks – including 38 million added since its previous study – and hashing them with MD5, researchers at security firm Kaspersky found that, using a single Nvidia RTX 5090 graphics card, 60 percent of passwords could be cracked in less than an […]
https://rbfirehose.com/2026/05/10/the-register-60-of-md5-password-hashes-are-crackable-in-under-an-hour/
60% of MD5 Password Hashes Are Crackable In Under an Hour - Slashdot
In honor of World Password Day, Kaspersky researchers revisited their study on the crackability of real-world passwords and found that 60% of MD5-hashed passwords could be cracked in under an hour with a single Nvidia RTX 5090, and 48% could be cracked in under a minute. "The bottom line is that pas...
Ars Technica: Google bumps up Q Day deadline to 2029, far sooner than previously thought. “Google is dramatically shortening its readiness deadline for the arrival of Q Day, the point at which existing quantum computers can break public-key cryptography algorithms that secure decades’ worth of secrets belonging to militaries, banks, governments, and nearly every individual on earth.”
https://rbfirehose.com/2026/04/01/ars-technica-google-bumps-up-q-day-deadline-to-2029-far-sooner-than-previously-thought/
Ars Technica: Google bumps up Q Day deadline to 2029, far sooner than previously thought
Ars Technica: Google bumps up Q Day deadline to 2029, far sooner than previously thought. “Google is dramatically shortening its readiness deadline for the arrival of Q Day, the point at whic…
Trust without identity: hashes and signatures
https://negativepid.blog/trust-without-identity-hashes-and-signatures/
#trust #hashes #signatures #Cybersecurity #onlineSecurity #Internet #tech #IT #science #STEM #computing #AI #innovation #negativepid
Trust without identity: hashes and signatures
https://negativepid.blog/trust-without-identity-hashes-and-signatures/
#trust #hashes #signatures #Cybersecurity #onlineSecurity #Internet #tech #IT #science #STEM #computing #AI #innovation #negativepid
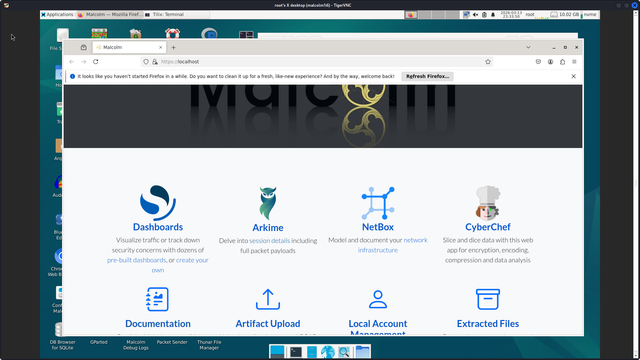
running malcom but the old malcolm - need to image and install latest - sort of dread going from debian to ubuntu but if i image i can revert easily. maybe they figured out updating, i don't want github only updates.
anyways it is a good one to offer vs say security onion - they use the same components mostly, suricata, zeek, elastic, maybe he has a live iso like last time.
i think the reason to go to ubuntu is better newer drivers, bigger dev base? as long as it works - that is my concern, avoid dependency hell and breakage.
it is good with managing all the containers and space for /datastore #sigs #hashes #dpi #netflow #ntop-ng #tcp-replay #binaries #hashcat
#Development #Pitfalls
Oops, my UUIDs collided! · How Universally Unique Identifiers can collide https://ilo.im/1682w2
_____
#Identifiers #Collisions #UUID #Mistakes #Attacks #Hashes #JavaScript #WebDev #Frontend #Backend