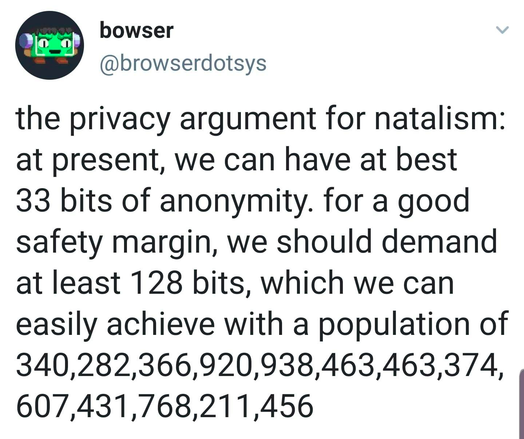
Think of online anonymity as being one person in a vast crowd. Every piece of personal information you reveal reduces the size of that crowd, the group of people you could plausibly be. For example, revealing your gender cuts the number of potential identities roughly in half.
One way to regain some anonymity is through deliberate disinformation. Suppose you share \(n\) independent yes/no facts about yourself, but intentionally flip \(k\) of them (without the attacker knowing which). In that case, you increase the number of identities consistent with your answers by a factor of \(C(n,k)\).
#OnlinePrivacy #DigitalAnonymity #InformationSecurity #CyberAwareness #PrivacyMatters #DigitalFootprint #DataProtection #InformationTheory #Anonymity #PrivacyEngineering #DataAnonymization #Disinformation #Combinatorics #SecurityResearch #ThinkBeforeYouShare #OnlineIdentity #PrivacyByDesign #DigitalEthics #ProtectYourData #InternetSafety #Privacy #CyberSecurity #Infosec #DataPrivacy #OnlineSafety #SecurityMindset