📢 2026 : 12 CVE activement exploitées, 4 absentes du catalogue CISA KEV selon Proofpoint
📝 ## 🔍 Contexte
Publié le 27 mai 2026 par la Proofpoint Emerging Threats Team, ce rapport s'ap...
📖 cyberveille : https://cyberveille.ch/posts/2026-05-27-2026-12-cve-activement-exploitees-4-absentes-du-catalogue-cisa-kev-selon-proofpoint/
🌐 source : https://www.proofpoint.com/us/blog/threat-insight/more-cves-same-playbook-2026-vulnerability-exploitation-wild
#APT28 #CVE_2026 #Cyberveille
2026 : 12 CVE activement exploitées, 4 absentes du catalogue CISA KEV selon Proofpoint
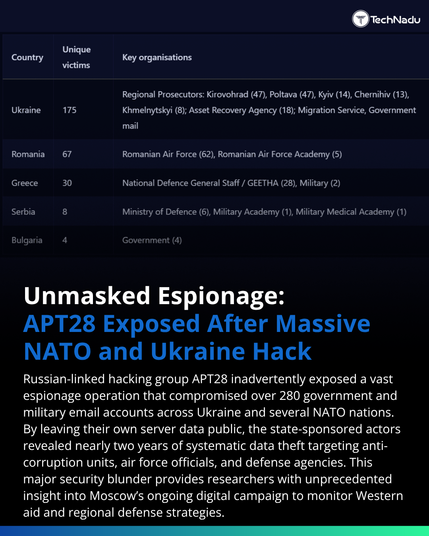
🔍 Contexte Publié le 27 mai 2026 par la Proofpoint Emerging Threats Team, ce rapport s’appuie sur deux flux de télémétrie : la surveillance des emails ciblés (centaines de millions de messages quotidiens) et un réseau de plus de 5 000 capteurs réseau ayant généré plus de 3 millions d’alertes en 2026. L’article dresse un bilan de l’exploitation des CVE 2026 dans la nature. 📧 Télémétrie email : 3 CVE weaponisées CVE-2026-21509 (Microsoft Office, RCE via RTF/OLE) : weaponisée par TA422 (APT28) dans les 24 heures suivant sa divulgation publique en janvier 2026. Ciblage d’agences gouvernementales ukrainiennes et d’entités européennes (défense, transport, diplomatie) via spear-phishing avec leurres institutionnels haute fidélité. La chaîne d’infection aboutit au backdoor NotDoor Outlook et aux implants Covenant Grunt. L’infrastructure C2 utilise filen.io comme service de stockage cloud.