Links to a fresh set of "road toll" scam websites were pushed out by SMS today, targeting people with mobile phones in #Colorado area codes. The messages tell the recipient that they owe back tolls for driving on a highway in Colorado and purports to link to the Colorado DMV website. The page that loads accurately mimics the Colorado Department of Revenue website appearance, and claims you owe $6.69 in tolls. Needless to say, this is fake. Spread the word: Tolls are not collected directly via SMS message.
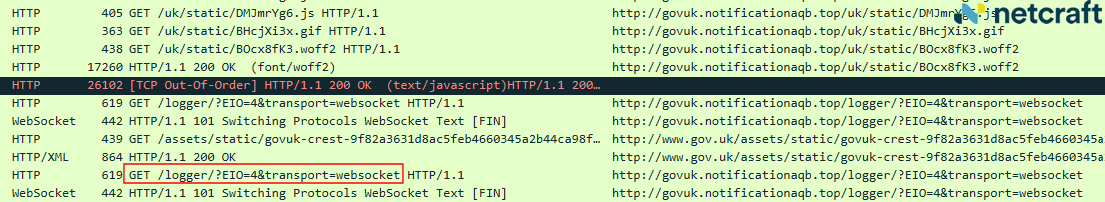
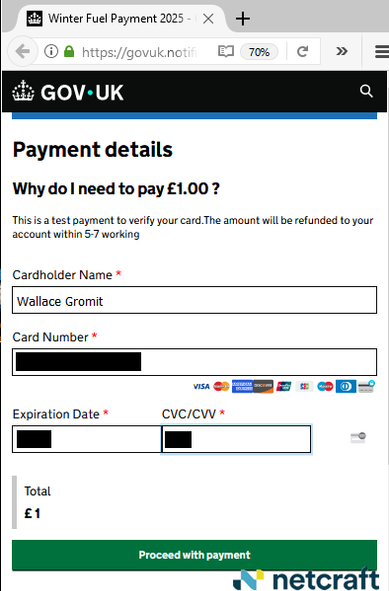
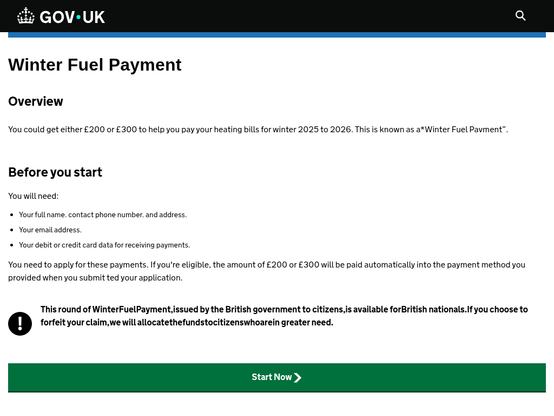
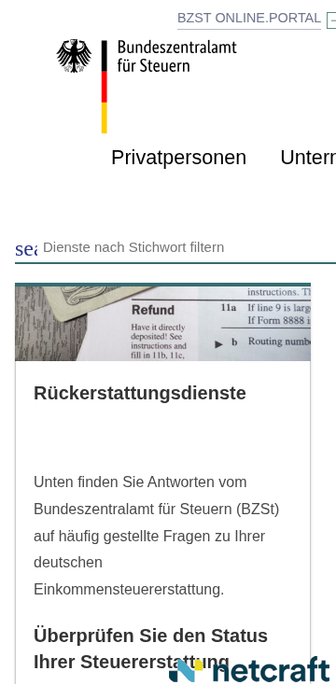
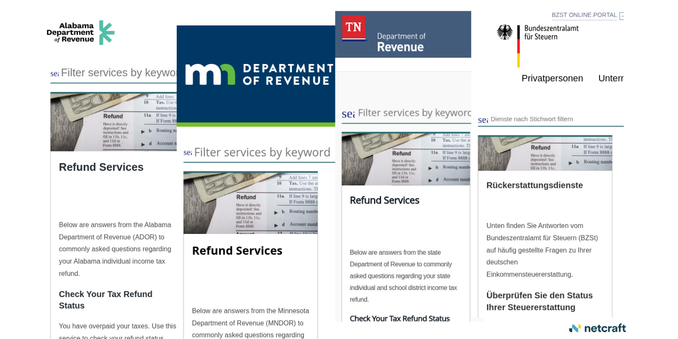
This is a continuation of an ongoing, Russia-originated campaign that has been targeting specific states and regions for the past year. I blogged about it in October for @Netcraft - we gave the threat actor the moniker Logger EIO. https://www.netcraft.com/blog/taxpayers-drivers-targeted-in-refund-and-road-toll-smishing-scams
#smishing #phishing #colorado #CODOR #CODMV #DMV #scam #fraud #roadtoll #tollroad #tollscam #LoggerEIO