Fuck those miserable, predatory parasites, fuck, fuck, fuck them.
Paul
- 9 Followers
- 117 Following
- 86 Posts
Fuck those miserable, predatory parasites, fuck, fuck, fuck them.
Signal has been running on Signal video for a long time, and the addition of call links about a month ago was a MASSIVE quality of life improvement.
Seriously, give them a try! Imagine, not sharing the contents of your daily standup with a large video conferencing company!
Europe followed the US into Afghanistan. Then US voters elected Trump and he pulled the plug.
Europe let the US lead the defence of Ukraine. And now US voters have voted for Trump, who wants Putin to win.
Europe has centered it's security politics around a US led NATO, and American voters have now voted for Trump, who wants to pull out of NATO.
It is time for a stronger, more capable, and fully independent Europe.
For our generation, this is our Churchill moment — it is time to lead.
Someone wrote a cool blog post using RMML for building detections
Detecting RMMs using KQL · Frank Korving
Introduction This is a short write-up on using Kusto Query Language (KQL) to detect Remote Monitoring and Management (RMM) artefacts in your process- and network telemetry. It uses multiple open-source projects that aggregate and centrally collect information on available RMMs. Threat actors often make use of legitimate and well-known RMM solutions during real world intrusions. These remote access tools are typically used as initial access vectors after a successful social engineering campaign and then used as a beachhead into the compromised network to pivot, deploy new tooling or exfiltrate data.
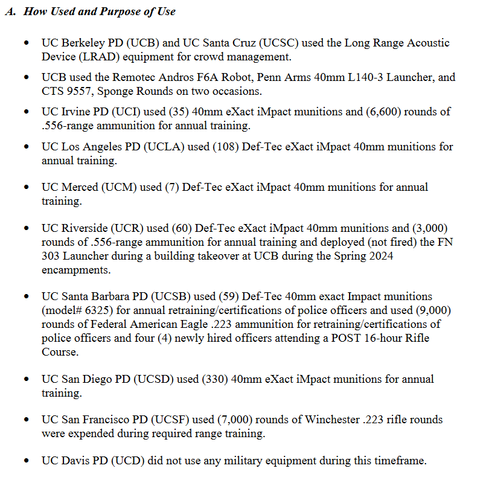
The European mind cannot comprehend this:
“The University of California just announced a list of military weaponry it wants in order to escalate its warfare on its students:
3000 rounds of pepper munitions
500 rounds of 40mm impact munitions
12 drones
9 grenade launchers
Read the full list here: https://regents.universityofcalifornia.edu/regmeet/sept24/c1.pdf “
Them: “You’re not trans, why are you always defending them?”
Me: “I am also not a domestic cat, and if I see you abusing one of those I’ll kick your ass too.”



 🇨🇦
🇨🇦