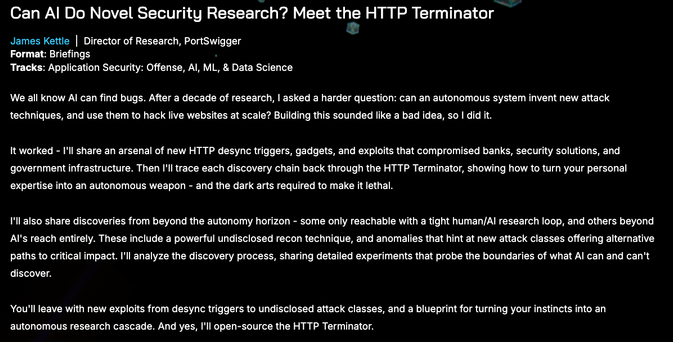
https://blackhat.com/us-26/briefings/schedule/?#can-ai-do-novel-security-research-meet-the-http-terminator-51894
Burp Suite
| Homepage | https://jameskettle.com/ |
| https://twitter.com/albinowax | |
| https://www.linkedin.com/in/james-kettle-albinowax/ | |
| PortSwigger | https://portswigger.net/research |