Saltmyhash
- 37 Followers
- 327 Following
- 724 Posts
(huntress.com) In-the-Wild Exploitation of Nightmare-Eclipse Privilege Escalation Tooling and BeigeBurrow Tunneling Agent Observed in Active Intrusion
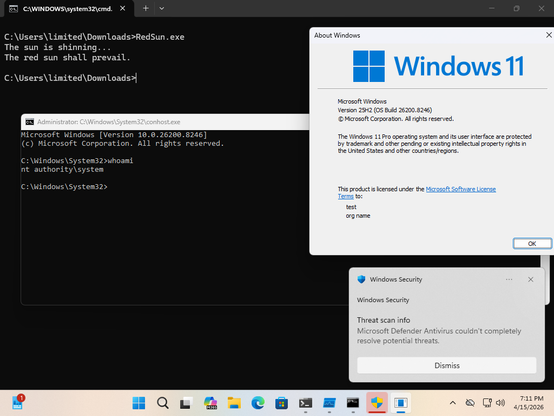
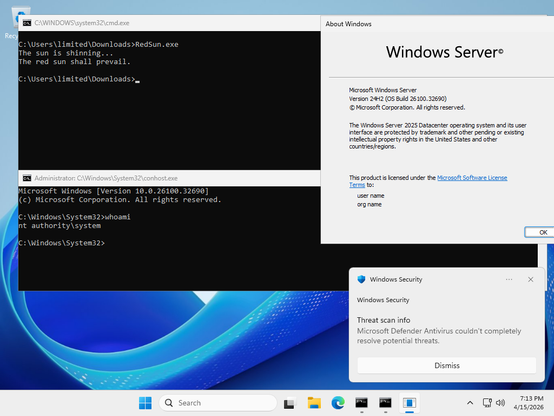
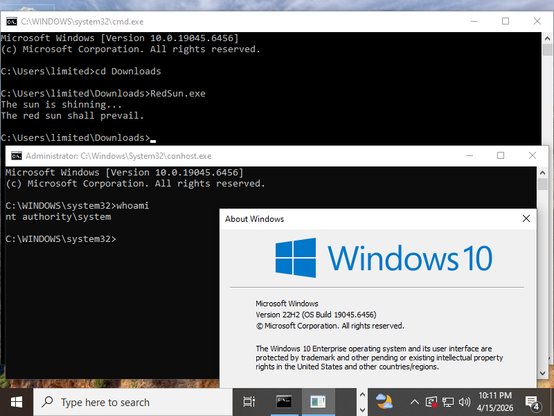
In-the-wild exploitation of Nightmare-Eclipse tooling (BlueHammer, RedSun, UnDefend) and BeigeBurrow tunneling agent observed in active intrusion. BlueHammer (CVE-2026-33825) exploits a TOCTOU race in Windows Defender for SYSTEM-level SAM credential theft; RedSun/UnDefend remain unpatched. Initial access via compromised FortiGate SSL VPN credentials, hands-on-keyboard recon, and Go-based yamux reverse tunnel (BeigeBurrow) for persistent C2.
In brief - Threat actor leveraged novel privilege escalation tools (BlueHammer CVE-2026-33825, RedSun, UnDefend) and BeigeBurrow reverse tunnel in a failed intrusion. Initial access via FortiGate SSL VPN, post-exploitation via M365Copilot.exe. Huntress terminated activity; hunt for IOCs.
Technically - BlueHammer abuses TOCTOU in Windows Defender with Volume Shadow Copy and process suspension for SAM database read. RedSun uses oplocks/directory junctions for arbitrary write via Storage Tiers Management Engine COM. UnDefend disrupts Defender via file locks. BeigeBurrow (Go/yamux) establishes multiplexed reverse tunnel to staybud.dpdns[.]org:443. Binaries staged in user-writable paths; recon commands spawned from M365Copilot.exe.
Source: https://www.huntress.com/blog/nightmare-eclipse-intrusion

Nightmare-Eclipse Tooling Seen in Real-World Intrusion | Huntress
Huntress observed in-the-wild use of Nightmare-Eclipse tooling, including BlueHammer, RedSun, and UnDefend, in a live intrusion involving FortiGate VPN compromise as the initial access, reconnaissance commands, and likely tunneling activity.
(zscaler.com) Payouts King Ransomware: Technical Analysis of a BlackBasta Successor Group
New ransomware group Payouts King, linked to former BlackBasta affiliates, emerged in April 2025 with advanced TTPs and evasion techniques.
In brief - Payouts King, a BlackBasta successor, uses spam bombing, Microsoft Teams abuse, and Quick Assist for initial access. The group employs robust encryption, anti-EDR measures, and operates a Tor-based data leak site. Zscaler ThreatLabz provides IOCs and TTPs for detection.
Technically - Payouts King ransomware uses stack-based string obfuscation, FNV1/CRC32 hashing for API resolution, and command-line argument obfuscation. File encryption leverages RSA-4096 and AES-256-CTR via OpenSSL, with per-file keys and partial encryption for performance. EDR/AV evasion includes direct Zw* system calls (e.g., ZwTerminateProcess) resolved via ntdll export table walking. Persistence is via scheduled tasks, and forensic artifacts are removed by deleting shadow copies and clearing logs.
Source: https://www.zscaler.com/blogs/security-research/payouts-king-takes-aim-ransomware-throne
From the same author as BlueHammer we now have RedSun.
This works ~100% reliably to go from unprivileged user to SYSTEM against Windows 11 and Windows Server 2019+ with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled. Any system that has cldapi.dll should be affected.
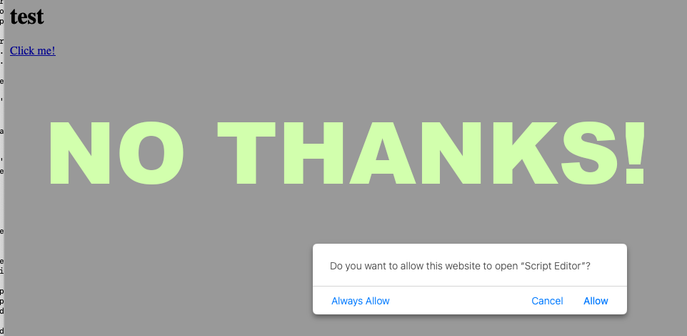
After working on it a bit, we have a fix for a recent #ClickFix attack against #macOS that leverages AppleScript. Here's the writeup, and a link to the forum thread!
NotNullOSX macOS stealer TTPs which seem unique from other commodity macOS infostealers:
Block or alert on outbound connections to mactest-6b2ab-default-rtdb[.]firebaseio.com.
Flag persistent text/event-stream (SSE) connections from macOS endpoints.
Alert on Mach-O binaries downloaded from cdn.filestackcontent[.]com.
Monitor for LaunchAgents with plaintext credentials in EnvironmentVariables.
Flag dscl . -authonly calls from non-system processes
Alert on xattr -rd com.apple.quarantine invoked from browser or document context
Review any Full Disk Access grants to unrecognized applications.
Check /tmp for staged, short-lived Mach-O binaries, especially with names matching the module naming convention (*Grab, ReplaceApp).
Alert curl fetching a binary from a not known/familiar domains followed immediately by xattr -d com.apple.quarantine
https://moonlock.com/notorious-hacker-returns-notnullosx-stealer
10,000 Chicago Concert Recordings Are Being Uploaded to the Internet Archive: Nirvana, Phish, Sonic Youth, They Might Be Giants & More
10,000 Chicago Concert Recordings Are Being Uploaded to the Internet Archive: Nirvana, Phish, Sonic Youth, They Might Be Giants & More
Perhaps you've had the experience of moving to a new city and immediately being told that you've missed its golden age of live music. To an extent, this has happened in more or less every period of the past fifty or sixty years.
 🛡️
🛡️