I built a custom Microsoft Sentinel data connector with no Azure Functions, Logic Apps, or compute costs.
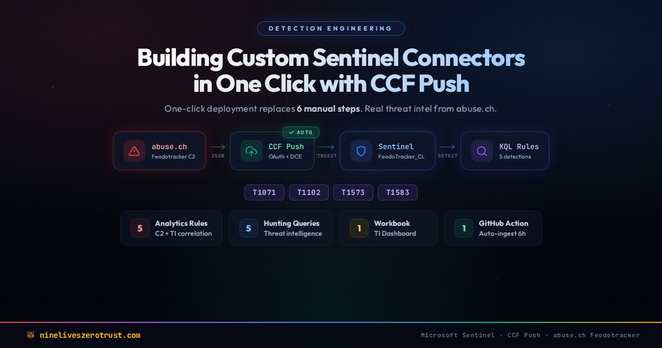
Custom connector development in Sentinel has always meant wiring up a DCE, DCR, a custom table, an Entra app, a client secret, and RBAC just to start ingesting data. CCF Push mode changes that. With one click in the Data Connectors gallery, Sentinel provisions all of that for you.
I tested it with abuse.ch Feodotracker, a free feed tracking live botnet C2 infrastructure. No synthetic data, no toy examples.
- 4 JSON connector artifacts and a Python sender using OAuth 2.0
- 5 KQL analytics rules mapped to MITRE ATT&CK
- 5 hunting queries and a Sentinel workbook
- GitHub Actions ingestion every 6 hours at zero compute cost
The detection I'm most proud of is a KQL rule that joins C2 IPs against your live network traffic to answer one question: is any device in my environment talking to a confirmed botnet C2 server?
If you're still using the legacy Data Collector API, heads up. It retires September 14, 2026. CCF Push is the path forward and honestly a massive improvement.
Everything is open source. Fork the repo, add your credentials, and you have a working threat intelligence connector.
Blog: https://lnkd.in/g5R_gee8
Repo: https://lnkd.in/g5whjgPw