I've done it! After literal months of work, I've finally finished my (rather long) blog post about how AES-GCM works and how it's security guarantees can be completely broken when a nonce is reused:
It includes more than 10 interactive widgets for you to try out AES-GCM, GHASH and the nonce reuse attack right in your browser! (Powered by #RustLang and #WASM )
If you're interested in #cryptography , #math (or #maths ) or #infosec you might find it interesting.
If you do read it, I'm all ears for feedback and criticism!


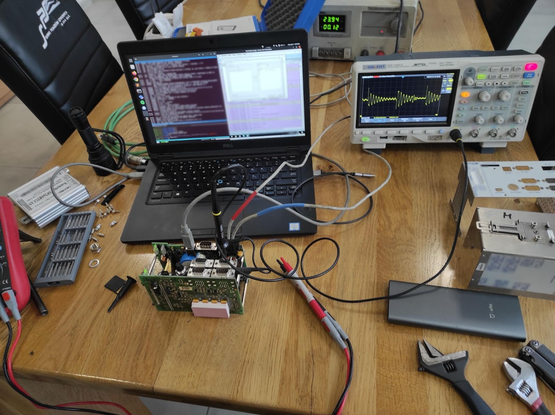


 Shlee messed around &
Shlee messed around &