| Pronouns | he/him |
| Signal | fre.99 |
| GitHub | https://github.com/frereit |
| Blog | https://frereit.de |
Frederik
- 210 Followers
- 403 Following
- 163 Posts
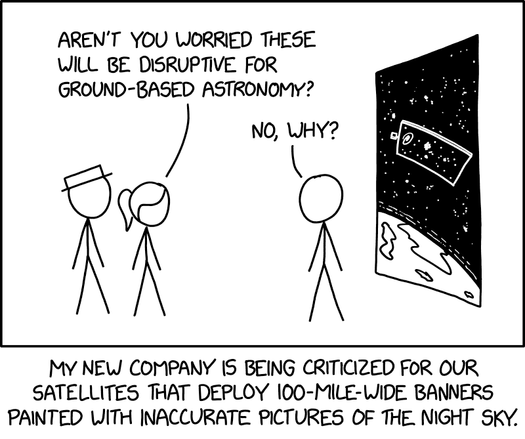
https://xkcd.com/3225/
Today I learned about flare.io, a company that provides other companies with detailed intel about data leaks affecting them.
Here's the catch: Unlike @haveibeenpwned or even intelx, they store everything that they can get their hands on. During a live demo, they proudly pulled up all email/password pairs that they have for a company that is not one of their customers, showed off how it saves not just the combo but everything the infostealer got, including all browser cookies and a screenshot of the personal machine of an affected employee.
So many things wrong with this..
- We just told them which company to look up, no verification at all.
- Bringing a demo laptop logged in to a "full admin" account that can see all data that they have access to, to a conference stand
- Storing a screenshot of a personal machine from an employee is absolutely not okay.
- and so much more...
When asked about legalities, they claim "it's based on needing to know this information for the companies" and falsely claimed "haveibeenpwned does the same thing, they also sell access to the combos" 🫨
Anyway, i sent a GDPR request for my data (and subsequent deletion), let's see what happens.
#infosec #insomnihack #privacy
ETA: to be clear, this wasn't a one off demo, they do this demo for everyone that walks up to their stand, and we have strong reasons to believe that the cleartext passwords that they show anyone that asks are real passwords and not demo data.
@maxleibman in space, no one can hear you scream*
* Probably a PulseAudio problem, check stack exchange
#Rapid7 published some analysis of #malware likely dropped through the Notepad++ issue.
One of the loaders used by the malware is built with #Microsoft Warbird, a kernel-level code protection framework used by Windows. @cirosec blogged about how this framework could be abused a while back and also published a PoC on GitHub.
I'm one of the authors of that research. We included some thoughts on detection in the article but if there's any further questions about the technique or anything, ask away :)
Today, Mandiant released a NetNTLMv1 Rainbow Table.
The rainbow table is relatively small, which increases the lookup time.
They say
The release of this dataset allows defenders and researchers to recover keys in under 12 hours using consumer hardware costing less than $600 USD.
This seems maximally useless, since you can already brute force NetNTLMv1 using Cloud GPUs for less than $100 USD on-demand, in a similar time..
 🏴
🏴