Tarah Wheeler
- 10.7K Followers
- 60 Following
- 1.8K Posts
We welcome your feedback on our Torment Nexus policy. To keep discussion productive, we ask that you refrain from the following topics:
- The book, _Don't Build the Torment Nexus_
- The literary use of the Torment Nexus as a cautionary tale
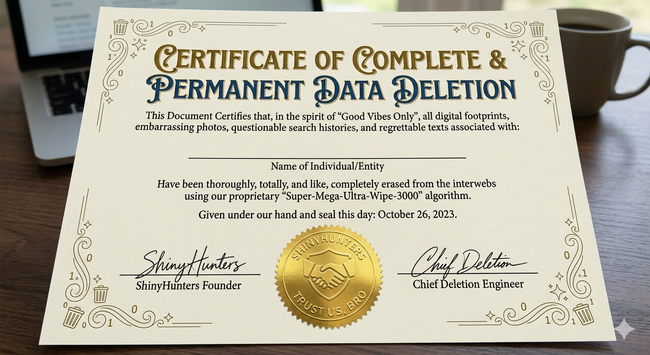
Happy ninth anniversary of my-butt-is-numb-and-I-haven't-moved-in-thirteen-hours-and-the-purple-and-orange-carpet-of-this-Orlando-convention-center-is-my-new-home-and-everyone-around-me-has-sunk-to-the-ground-and-everyone-at-this-infosec-con-are-all-sharing-power-outlets-and-cannibalizing-each-others-analogies-for-our-bosses-who-don't-know-what-the-red-screen-means-and-think-the-name-ShadowHunters-is-some-science-fiction-shit-we-all-made-up-and-this-is-so-much-worse-than-we-can-explain-and-oh-god-those-poor-people-in-England day.
#WannaCry 12 May, 2017.
RE: https://infosec.exchange/@Tarah/116540734885717411
They’re operational again as of 14m ago.
NEW: Polish intelligence says hackers broke into 5 water treatment systems, and could have tampered with the safety of water supply.
Poland did not accuse Russia for these attacks, but it said the Russian government has been targeting military and civilian infrastructure — a threat the U.S. and other Western countries face too.
📣 Today at 4PM CT on Blue Team Con Online - Amanda Draeger shows you how costs are calculated for cyber incidents, and how you can use this information to get the budget you need.
Learn more: https://blueteamcon.com/blue-team-con-online
Join on YouTube: https://btcon.link/youtube
Join on Twitch: https://btcon.link/twitch