Notepad++ have released a new version to fix the auto update process being hijacked https://notepad-plus-plus.org/news/v889-released/
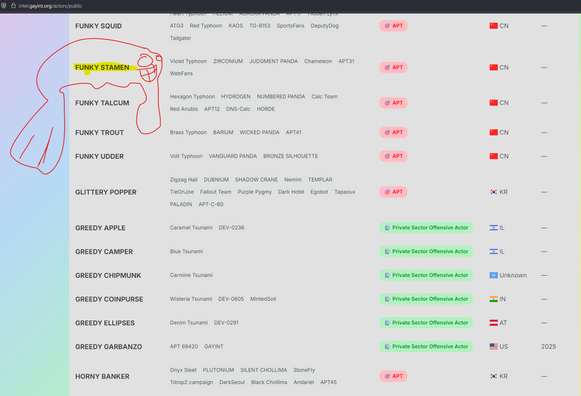
I reported the vulnerability, it is being hijacked by threat actors in China. https://doublepulsar.com/small-numbers-of-notepad-users-reporting-security-woes-371d7a3fd2d9







 🇺🇦
🇺🇦
 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉
