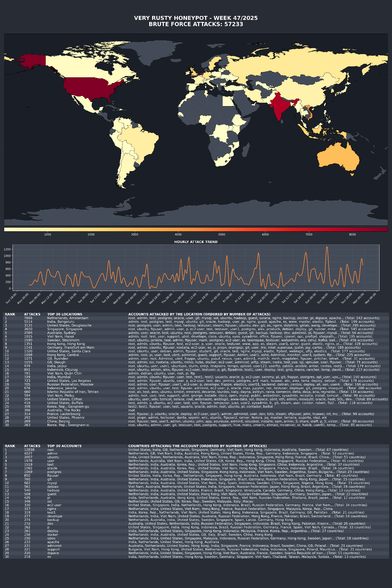
SSH brute force login attempts 🤣 It is time to hide your ssh port behind a vpn? I say, disable password based login and only use the 2FA protected ssh keys based login and ensure TCP/port 22 is rate limited.
I've more tips for you. Read: OpenSSH Server Best Security Practices https://www.cyberciti.biz/tips/linux-unix-bsd-openssh-server-best-practices.html if you want to protect yourself from such attacks.