💡𝚂𝗆𝖺𝗋𝗍𝗆𝖺𝗇 𝙰𝗉𝗉𝗌📱 (@[email protected])
Attached: 1 image 1/3 #TechTuesday #Password I have a #TechTip for you this week about how to create memorable, #Strong #Passwords such as a mix of letters and numbers, at least 1 uppercase, at least 1 special character, etc. I got this one from a video by an actual hacker. He said to think of a memorable sentence, and abbreviate it into a password. So, a sentence like "My birthday is the 29th of February!" abbreviates to "Mbit29thoF!". So it's strong, and easy to remember! But that's only the start...
@chucker @codinghorror
"that’s good advice for your master password" - every password, all of them unique and memorable
"you shouldn’t even _know_ the password" - what's wrong with being the only person in the whole word who knows your own passwords, none of which are written down or stored anywhere at all? 😂
@SmartmanApps @codinghorror making a password memorable decreases its entropy. A random password you don't have to memorize can be longer.
That's why only the passwords you really _have_ to type in by hand should be memorable.
@chucker @codinghorror
"A random password you don't have to memorize can be longer" - the only limit to the length of this one is your own imagination.
"That's why only the passwords you really _have_ to type in by hand should be memorable" - yep, solved problem. Did you even read the thread?
@SmartmanApps your thread says:
>So what we want to do is follow this same process for each place and have a memorable strong password for that place.
Do not create memorable passwords for "places". Use a password manager.
"Do not create memorable passwords for "places". Use a password manager" - in other words, you can't fault anything I said at all. Do you have shares in a password manager company or something? My storage is free - it's me 🙂
And how many uniquely memorable passwords do you have to remember and not screw up? In this blog by Troy Hunt, he estimated he had 130 accounts back in 2011. https://www.troyhunt.com/im-sorry-but-were-you-actually-trying/
I’m sorry, but were you actually trying to remember your comical passwords?
I love a good XKCD comic; Randall Munroe has a unique way of cutting right to the crux of technology issues and always doing it in a humorous fashion. Little Bobby Tables [http://xkcd.com/327/] remains an all-time classic and it’s amazing how many times you’ll see
It doesn't matter how many there are when you can remember all of them. That's the beauty of it. Screwing them up only happens when they're not memorable. None of the problems he mentions are actually problems with this technique. Numbers only? Pick a sentence as usual, use the number of letters in each word. You know Troy is sometimes sponsored by password managers, right? "This is based on what I have configured in 1Password – one of the leaders in password management"
@bob_zim @chucker
"No, this is terrible advice" says person who can't come up with a single reason why it's "terrible".
"As Sören said" - who also couldn't come up with a single reason why this was "terrible".
"then all further passwords should be randomly generated" - they are. Dynrtt? (Did you not read the thread?)
"made up of dictionary words which I selected randomly, then memorized" - or you can just pick 1 memorable sentence to begin with! (Ycjp1mstbw!)
@bob_zim
"After reading some of that account’s recent posts, they are similarly wrong" - says person who demonstrably stopped reading before coming to the MATHS TEXTBOOKS which prove it's all correct. All posts from this account are factual. I'm a Maths teacher
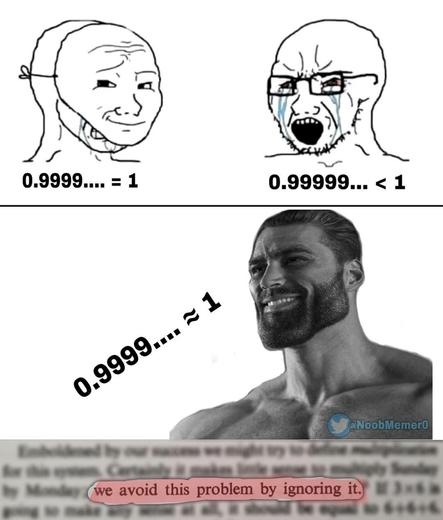
"which the poster asserts equals 1" - as do Maths textbooks and calculators
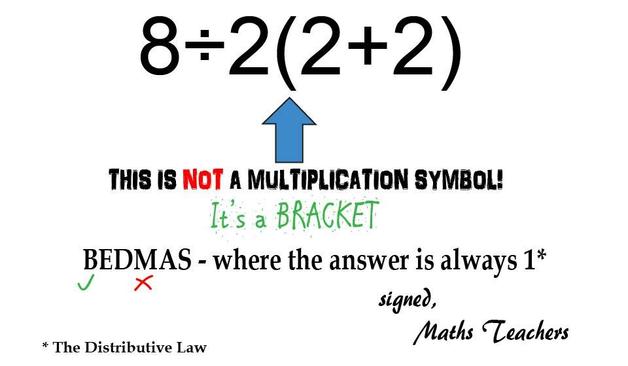
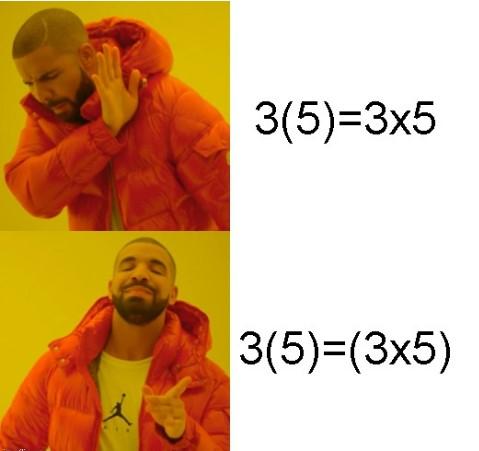
"parens resolve first yielding 8/2*4" - no, they yield 8/(2x4)=8/8
"then multiplication and division" - there is no multiplication, only brackets and division
@bob_zim
In other words, you disobeyed both The Distributive Law and the order of operations rules, hence your wrong answer
"depends on operating only in the space of real numbers" - we're not doing any operations, we are simply writing an infinitely recurring decimal. False equivalence argument, which you would know if you kept reading
"in the system of hyperreals, 0.9… exactly equals 1" - we're still not doing any operations with it. It's still equal to infinitely recurring 9's, not 1.
P.S. good on you for blocking me before giving me a chance to fact-check your replies directly
@SmartmanApps @chucker No, this is terrible advice. As Sören said, you should create one password for a password manager, then all further passwords should be randomly generated and stored in that password manager. This has been standard advice in the security community for about 20 years. Password length is much more important than the variety of characters used.
As someone who deals with authentication security for a living, my master password is around 50 characters long and is made up of dictionary words which I selected randomly, then memorized.
@chucker After reading some of that account’s recent posts, they are similarly wrong. I now suspect it to be some kind of troll. For example:
https://dotnet.social/@SmartmanApps/112711027003047449
The provided example with the division and parens is 8/2(1+3), which the poster asserts equals 1. No, it equals 16. The parens resolve first yielding 8/2*4, then multiplication and division resolve at the same time, left to right.
Similarly, the assertion 0.9… it not equal to 1 depends on operating only in the space of real numbers, and 0.9… is not a real number. It’s a hyperreal, and in the system of hyperreals, 0.9… exactly equals 1.
💡𝚂𝗆𝖺𝗋𝗍𝗆𝖺𝗇 𝙰𝗉𝗉𝗌📱 (@[email protected])
Attached: 1 image 1/6 This #MathsMonday I want to cover a new storm I've seen brewing, but first I want to go over again the motivation for these #Maths posts... On one hand it's to provide me (and you!) with things that can be linked to, to save myself (and you) from repeating myself, but peeling back the onion on that really it's about preventing #Math #bullying, for sadly I have seen people who bully others into believing the wrong #Mathematics answer. i.e. not about who's right, but stopping the #bullies!...
@codinghorror Holy cow, look at that list. A) Someone must have worked hard to come up with it. And then B) Some programmer must've worked even harder to implement all of these checks.
And neither of these persons said "Fuck this shit".
Also, neither of these persons had any relationship to security engineering, or they would've pointed at NISTs SP 800-63B.
They forgot "must not include numbers from your birthdate"
" You password must match /^$w^[w]+[$¥√$(=${q,}(?=©)/"
Migration support is coming
@codinghorror the way most corporations handle passkeys is awful and a setback, not progress. amazon wants me to enter a totp even when i use a passkey. amazon, microsoft, etc. are gunking up my yubikey's slots with their single-provider ("resident") passkeys, whereas nextcloud can do webauthn without using up a slot. most users do not have dedicated hardware, so losing their phones, upgrading their phones, losing access to their google/microsoft/apple/... accounts will lock them out of their other accounts and prevent them from switching platforms (ios, android, windows), further cementing tech giants' influence.
unless you can explain how passkeys work, and where they are stored, and how you can export and backup them, you should stick with passwords. the rules described in your example are obviously terrible, though.
@codinghorror
Someone should create a metadata / microtagging standard that can be used to communicate the specific password requirements. Then everyone would implement it and password generators could create working and secure passwords.
…
Yes, I’ll see myself out now.
@iamlayer8 @codinghorror A machine-readable list of password rules has been proposed as a new well-known URI a few times. Services in a position to publish well-known URIs are generally also in a position to move to passkeys anyway, so it hasn’t gotten much traction.
At least this exists. The “quirks” directory has password rules for some popular sites:
GitHub - apple/password-manager-resources: A place for creators and users of password managers to collaborate on resources to make password management better.
A place for creators and users of password managers to collaborate on resources to make password management better. - apple/password-manager-resources