Three new CVEs for Cisco AnyConnect/ASA
CVE-2025-20333
CVE-2025-20363
CVE-2025-20362
Chained and under active exploitation since earlier in the year
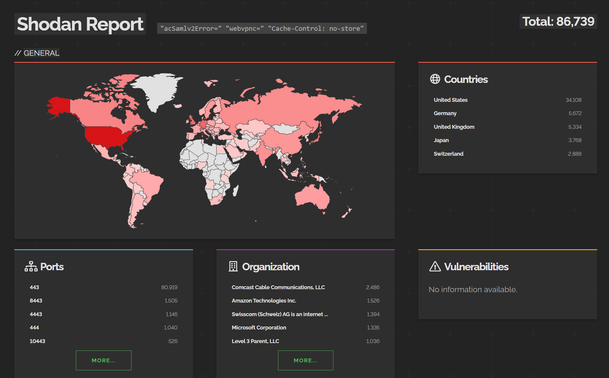
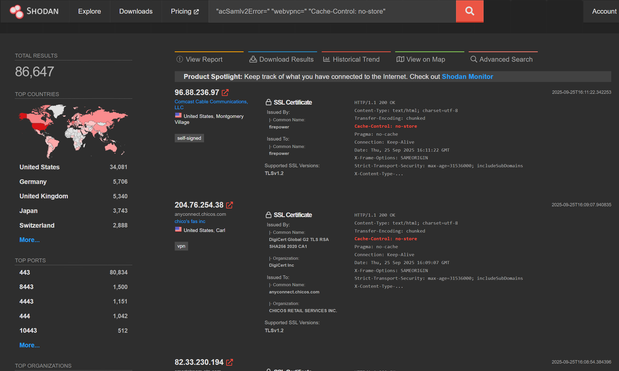
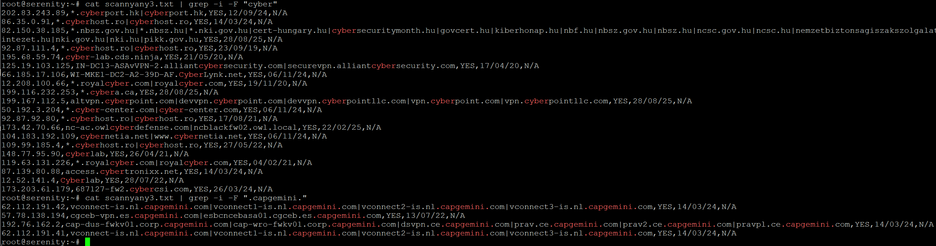
To find your org on .@shodan search for:
"acSamlv2Error=" "webvpnc=" "Cache-Control: no-store"
Then add org:YourOrg or ssl:YourOrg
25,000 IPs Scanned Cisco ASA Devices — New Vulnerability Potentially Incoming
GreyNoise observed two scanning surges against Cisco Adaptive Security Appliance (ASA) devices in late August including more than 25,000 unique IPs in a single burst. This activity represents a significant elevation above baseline, typically registering at less than 500 IPs per day.
Fixed versions, get to the ones highlighted in yellow ASAP as china goes double brr now
If you're on an unsupported ASA release you want to put it in the bin. If it didn't have secure boot, woops.
If anybody knows anybody at CISA, they have wrong/non-existent CVE on their executive order thingy, it's a typo that needs fixing. Edit: fixed.
With the Cisco blog, it reads like there is no problem.. but like, RCE vuln is RCE and still a problem.
Just because secure boot works (yay btw) doesn't mean there's no problem - of course they'll be no evidence on the box.
Interestingly, although the Cisco blog says the USG approached them in May 2025, the first vuln - CVE-2025-20333 - was fixed just over a year ago (around September 2024 product updates).
Another angle to that - it suggests a whole lot of orgs don't patch Cisco ASA edge devices. Which we already know from the Akira ransomware incidents -- which were using 5 year old vulns.
I've identified a way to establish if a box is vulnerable to #CyberWillyWave and started internet scanning, 90k boxes in progress.
Results probably at weekend if I'm bored or early next week.
Spoiler: a lot of orgs don't patch their Cisco edge devices. To be vuln to the full chain you have to be over a year behind with updates... and most orgs are over a year behind.
From #CyberWillyWave scanning at weekend:
45210 ASAs with WebVPN enabled
1250 ASAs patched for all three CVEs
43960 vulnerable ASAs remaining
97.24% remain vulnerable
Scans rerunning
The good news with that one btw is it's unlikely to become a thing e-crime groups exploit as it's too technically complex, it's just nation state espionage - so the operational impact should be low.
The bad news is that as e-crime groups become more rich, they may invest in AnyConnect exploits - if you paid something like $2m for an ASA exploit, you'd make it back no problem, even if an n-day as almost nobody patches.
*.gov.uk is less than 1% patched btw, many of the systems haven't been patched for years - the dates are firmware versions. The US federal government is only marginally better. I'm guessing orgs don't even know where they have ASA.
The plan is to start publishing the data publicly since I don't think anybody has an understanding of what the real world looks like.
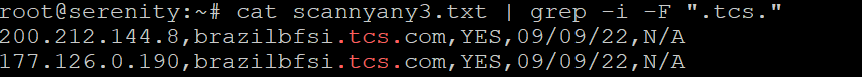
My Cisco ASA firmware versions scan is now public: https://github.com/GossiTheDog/scanning/blob/main/Cisco-ASA-firmware-updates-CVE-2025-20333-CVE-2025-20363-CVE-2025-20362.csv
Fields:
IP,hostnames,FirmwareVersionKnown,FirmwareModifiedDate,Errors
Dates are UK date format - DD/MM/YY
If FirmwareModifiedDate is below */08/25 or */09/25, the device is vulnerable to #CyberWillyWave as the firmware was complied August 2025 or later.
New scan running now, results at weekend.
It gives you a very good indication as to how regularly orgs patch, e.g.
My Cisco ASA firmware versions scan is now updated: https://github.com/GossiTheDog/scanning/blob/main/Cisco-ASA-firmware-updates-CVE-2025-20333-CVE-2025-20363-CVE-2025-20362.csv
Fields:
IP,hostnames,FirmwareVersionKnown,FirmwareModifiedDate,Errors
Dates are UK date format - DD/MM/YY
If FirmwareModifiedDate is below */08/25 or */09/25, the device is vulnerable to #CyberWillyWave as the fixed firmware was complied August 2025 or later.
New scan running now, results at midweek.
Patch rates are still below 20%.
Edit: #CyberWillyWave
My Cisco ASA firmware versions scan is now updated: https://github.com/GossiTheDog/scanning/blob/main/Cisco-ASA-firmware-updates-CVE-2025-20333-CVE-2025-20363-CVE-2025-20362.csv
Fields:
IP,hostnames,FirmwareVersionKnown,FirmwareModifiedDate,Errors
Dates are UK date format - DD/MM/YY
If FirmwareModifiedDate is below */08/25 or */09/25, the device is vulnerable to #CyberWillyWave as the fixed firmware was complied August 2025 or later.
New scan running now, results at weekend.
Patch rates are at 22% complete, two weeks in.
Y'all probably want to patch.
If anybody is wondering, number of Cisco ASA devices with WebVPN enabled with their firmware year:
2025 - 10570
2024 - 12428
2023 - 3888
2022 - 4594
2021 - 3951
2020 - 2076
The average is orgs are around 18 months behind with patching (for internet facing).
If anybody is wondering how these scans are generated - one time @shodan search for AnyConnect boxes, export, then vibe coded scanner that fingerprints firmware creation date using the SSL applet and outputs to CSV.
About 40% of orgs are missing from results as they are clientless.
There’s much better ways of doing it.
Those Cisco ASA vulns continue to be patched at a slow rate.
UK orgs, sign up for the NCSC Early Warning system and actually patch your systems when notified.
https://www.ncsc.gov.uk/section/active-cyber-defence/early-warning
My Cisco ASA firmware versions scan is now updated: https://github.com/GossiTheDog/scanning/blob/main/Cisco-ASA-firmware-updates-CVE-2025-20333-CVE-2025-20363-CVE-2025-20362.csv
Fields:
IP,hostnames,FirmwareVersionKnown,FirmwareModifiedDate,Errors
Dates are UK date format - DD/MM/YY
If FirmwareModifiedDate is below */08/25, the device is vulnerable to #CyberWillyWave as the fixed firmware was complied August 2025 or later.
New scan running now, results on probably Wednesday.
Patch rates are at 25% complete, two weeks in.
Y'all probably want to patch.
Btw - one observation from the #CyberWillyWave ASA data - less devices respond each time I scan. They’re not blocking me - the devices are just offline.
I know a few regional CERTs have been using the data to inform orgs to patch, I think what’s happening is orgs are finding they have old devices and are nuking them. I’m free attack surface management!
An observation from CVE-2025-20333 (Cisco ASA AnyConnect vuln) - orgs just don't patch ASA.
The patch rate is really, really poor - ransomware groups are likely going to reinvest in targeting Cisco ASA product security, even just n-days, as realistically tens of thousands of organisations are years behind with patching their edge VPN appliances -- it's an open door into the world's largest companies.
Upwards of 70% of orgs never patched this one - thankfully it's just China with the exploit.
Patching is a pain in the butt, requires an active Cisco maintenance contract and it's often deployed as a "set and forget" kind of solution.
They also likely lack the visibility and detections for when they have been owned.
Why am I not surprised?
Ah yes, cause I'm in incident response for a while and this is our default meme:
@GossiTheDog thanks, there’s some interesting ones in there like dc.vpn.cisco.com.
Just to double check my understanding, the list is everything running potentially vulnerable services and you need to filter out the patched ones from the list?
@GossiTheDog
Enterprises don't patch shit.
Srsly. My job is software for enterprise-scale storage systems, and all the data we get from the field says that our median customer is parked on a release from, like, 2018. They only upgrade if they do a hardware expansion and the new hardware is incompatible with the old release.
Because there's this attitude of "if you don't touch it, it won't break"
@GossiTheDog Aww... ASA. One of my favorites during the MPG security scan. ;-P
.oO( for some impressions: https://pure.mpg.de/pubman/faces/ViewItemOverviewPage.jsp?itemId=item_3532055 / https://doi.org/10.17617/2.3532055 )
@GossiTheDog I'm curious if any of the more offense-oriented feds are either thinking about(or have quietly already started) just unmanged service provider-ing unpatched friendly entities.
It'd almost certainly be legally dubious; but has to be someone at the NSA/GCHQ/etc who is just tearing their hair out knowing that someone is going to run the exploit; and if it were them they could either patch or brick to get the hole closed; while others will likely be worse.
The individual councils (bexley etc) are probably impossible for anyone to push, but you'd think *someone* should be looking after justice.gov.uk
@GossiTheDog To be fair, Cisco have an old reputation that it's unwise to change an IOS which has been found to be working.
Big C has improved a lot on this front, but they had decades to ingrain a disdain for touching the IOS unless absolutely necessary in any packet plumber.
@GossiTheDog ASA patches often broke things. Not great for 24/7 VPN tunnels or remote access to infrastructure. SOP was patch when CISA said the sky was falling. Then remediate all of the discrepancies between old/new and GUI/cli.
I don't use them any more, but still have old ones that really need to be recycled, lest they be re-purposed by some cheapskate (me included).
Same can be said for Sonicwalls. Especiallly small businesses without staff. Some MSPs won't patch them unless somebody screams about it.












 🇺🇦
🇺🇦

 @ Revision26
@ Revision26