Three new CVEs for Cisco AnyConnect/ASA
CVE-2025-20333
CVE-2025-20363
CVE-2025-20362
Chained and under active exploitation since earlier in the year
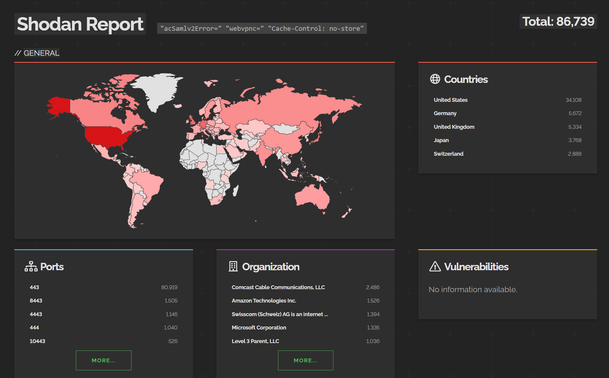
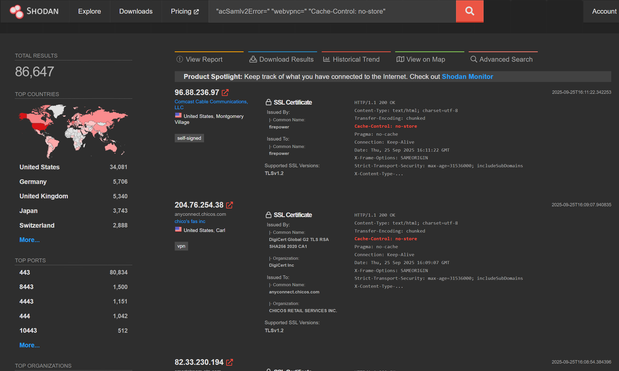
To find your org on .@shodan search for:
"acSamlv2Error=" "webvpnc=" "Cache-Control: no-store"
Then add org:YourOrg or ssl:YourOrg
25,000 IPs Scanned Cisco ASA Devices — New Vulnerability Potentially Incoming
GreyNoise observed two scanning surges against Cisco Adaptive Security Appliance (ASA) devices in late August including more than 25,000 unique IPs in a single burst. This activity represents a significant elevation above baseline, typically registering at less than 500 IPs per day.
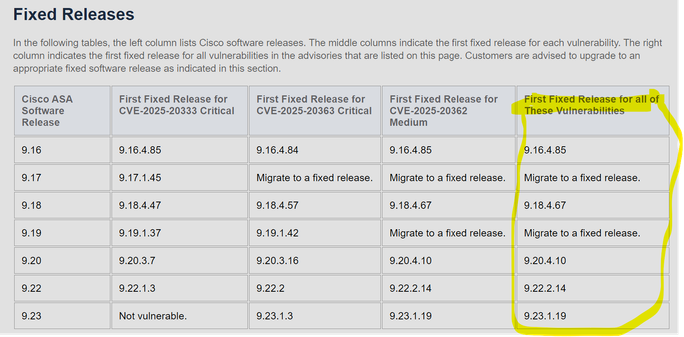
Fixed versions, get to the ones highlighted in yellow ASAP as china goes double brr now
If you're on an unsupported ASA release you want to put it in the bin. If it didn't have secure boot, woops.
If anybody knows anybody at CISA, they have wrong/non-existent CVE on their executive order thingy, it's a typo that needs fixing. Edit: fixed.
With the Cisco blog, it reads like there is no problem.. but like, RCE vuln is RCE and still a problem.
Just because secure boot works (yay btw) doesn't mean there's no problem - of course they'll be no evidence on the box.
Interestingly, although the Cisco blog says the USG approached them in May 2025, the first vuln - CVE-2025-20333 - was fixed just over a year ago (around September 2024 product updates).
Another angle to that - it suggests a whole lot of orgs don't patch Cisco ASA edge devices. Which we already know from the Akira ransomware incidents -- which were using 5 year old vulns.