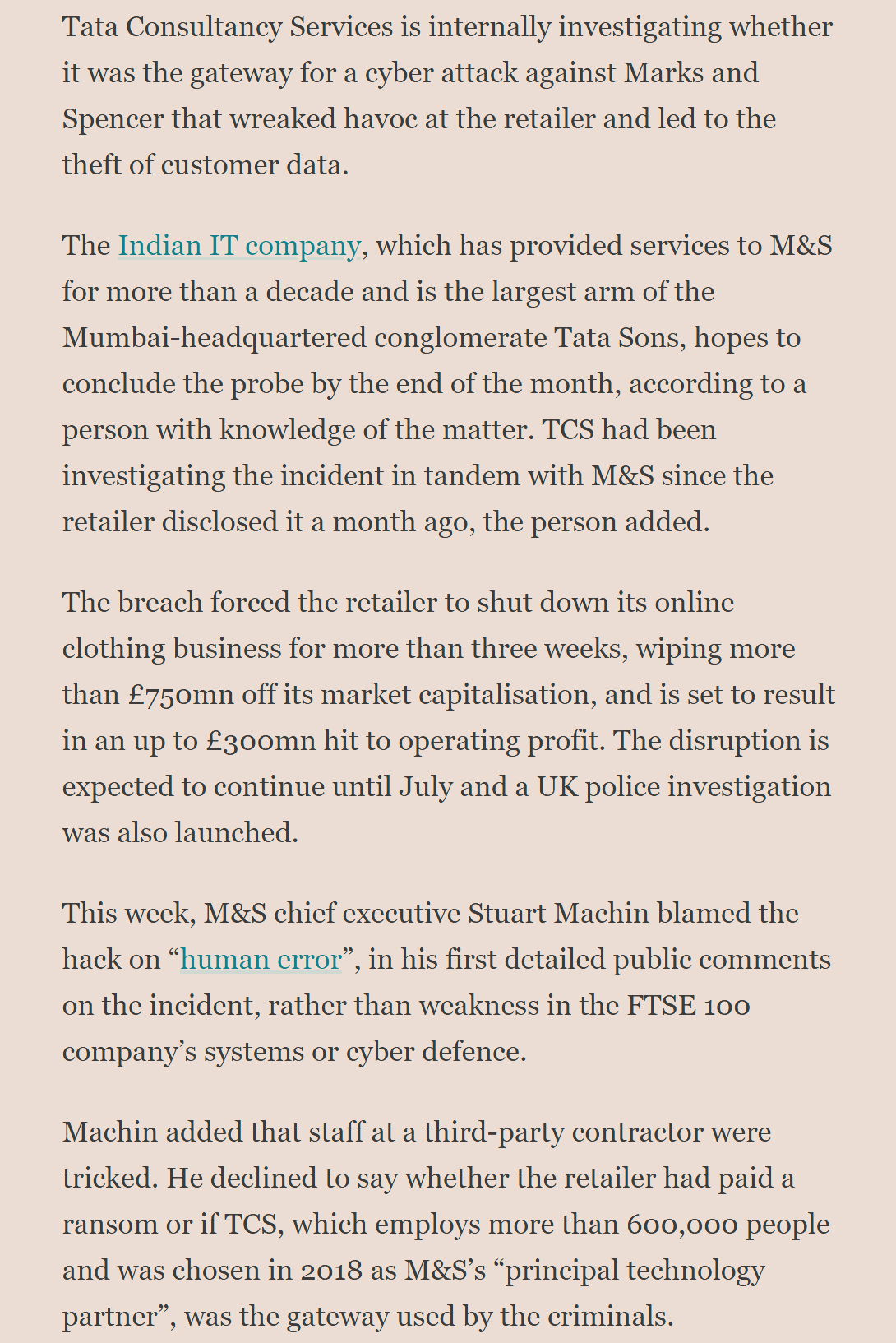
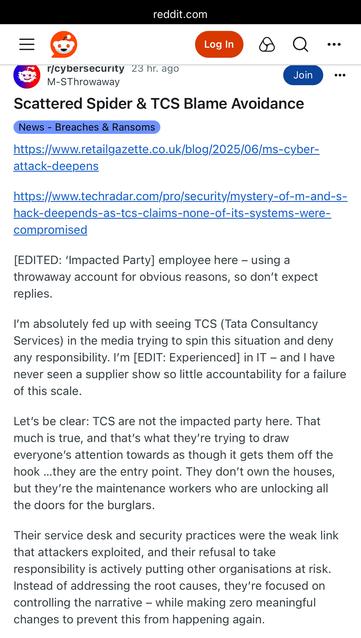
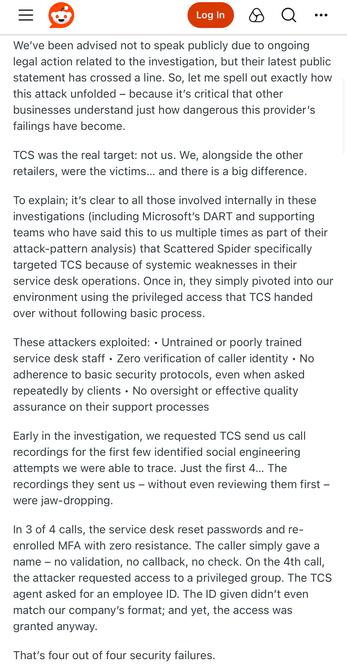
TCS has a security incident running around the M&S breach.
Interestingly the source claims TCS aren't involved in Co-op's IT - which is categorically false, they took over most of it while I worked there, including the helpdesk, and my team (SecOps) after I left.
https://www.ft.com/content/c658645d-289d-49ee-bc1d-241c651516b0








 🇺🇦
🇺🇦