Some fascinating research out on hacking a Subaru via STARLINK connected vehicle service.
"On November 20, 2024, Shubham Shah and I discovered a security vulnerability in Subaru’s STARLINK connected vehicle service that gave us unrestricted targeted access to all vehicles and customer accounts in the United States, Canada, and Japan.
Using the access provided by the vulnerability, an attacker who only knew the victim’s last name and ZIP code, email address, phone number, or license plate could have done the following:
Remotely start, stop, lock, unlock, and retrieve the current location of any vehicle.
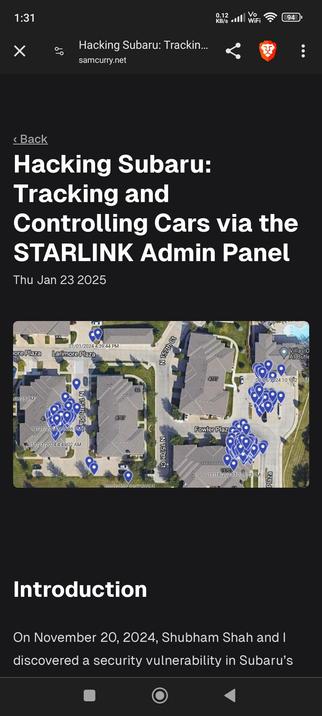
Retrieve any vehicle’s complete location history from the past year, accurate to within 5 meters and updated each time the engine starts.
Query and retrieve the personally identifiable information (PII) of any customer, including emergency contacts, authorized users, physical address, billing information (e.g., last 4 digits of credit card, excluding full card number), and vehicle PIN.
Access miscellaneous user data including support call history, previous owners, odometer reading, sales history, and more.
After reporting the vulnerability, the affected system was patched within 24 hours and never exploited maliciously."
Hacking Subaru: Tracking and Controlling Cars via the STARLINK Admin Panel
On November 20, 2024, Shubham Shah and I discovered a security vulnerability in Subaru’s STARLINK admin panel that gave us unrestricted access to all vehicles and customer accounts in the United States, Canada, and Japan.