They used Outlook Web App - runs the Exchange Server codebase btw - to craft tokens to bypass auth.
There's some clever wording in blog around only impacting OWA. OWA is a part of Microsoft 365 and Exchange Online.
The problem was discovered by the US Government and reported to Microsoft. https://edition.cnn.com/2023/07/12/politics/china-based-hackers-us-government-email-intl-hnk/index.html
This one looks like a huge mistake, a consumer MSA key (managed end to end by Microsoft - there's no external logs) was able to forge any Azure AD key.
It's only become public it appears as the US Government told Microsoft, which forces public disclosure.
CISA's advisory on the Microsoft 365 compromise is wayyyyyyyyyyy better than the Microsoft advisory - contains actionable hunting and logging information. Kinda nuts that the US Government are providing better information about Microsoft than Microsoft.
Okay - I found a victim org.
The situation for them is 😬
MS are going to have to release more info, methinks.. or I crank out the blog writing.
Really good Washington Post piece on the breach of Microsoft 365’s email service.
- hackers accessed customer emails for a month
- Microsoft didn’t notice
- USG had to tell them
- The access to generate tokens very likely came from MS being hacked and not realising
Talked to another impacted victim org in the Microsoft 365 hack, they basically got no actionable info from MS. Basically ‘lol you got hacked’ with wordsmithing and padding. 👀😬
I think I’m going to post hunting queries for this with an MS Paint logo.
🎶 regulation 🎶
I agree with CISA here (and have publicly for years) - security access logs for customers own services shouldn't be locked behind E5 per user licensing.
Yes, it will cost Microsoft money in upsell. They're more profitable than a large portion of the UK economy; they can afford it.
I should also point out the reason Microsoft was able to tell orgs specifically that they'd be targeted even when they didn't have E5 is MS already store the logs anyway.
“We don’t have any evidence that the actor exploited a 0day." say Microsoft. Their first blog on this says “exploit” - so are MS saying they don’t patch vulnerabilities in their cloud? 🤔
Their latest blog also says “This was made possible by a validation error in Microsoft code” - which is a vulnerability. Which is a 0day as it was under exploitation before Microsoft knew of it existing.
Microsoft lying to media and customers is not a good look.
All it took was Exchange Online in GCC and GCC High getting breached
Non-E5 users to get some security log availability finally.
More details about the Microsoft 365 Exchange Online breach in this article.
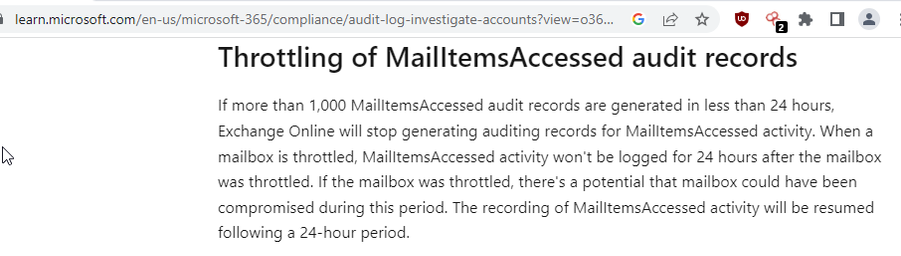
Although not stated, orgs are struggling to understand the scope of the breach due to audit log limits on MailItemsAccessed - it stops recording after 1k items. https://www.wsj.com/articles/u-s-ambassador-to-china-hacked-in-china-linked-spying-operation-f03de3e4
Just to loop this thread into this thread - I took a look at the attack path used in the M365 customer data breach.
A key part of the attack chain was documented by Microsoft at BlackHat in 2019.
Kevin Beaumont (@[email protected])
Attached: 2 images Been looking at Microsoft 365 email breach some more - it looks like Microsoft were aware of issues in same token validation space in Exchange Online 4 years ago. MS did a talk at BlackHat about it, after somebody external pointed out an invalid token allowed any email box to be accessed via consumer Outlook.com. They fixed that issue - but still allowed any valid MS token to access any email, so the threat actor stole one of the MSA certs. Talk: https://www.youtube.com/watch?v=KN6e1mqcB9s
Wiz have an in-depth look at what they think happened at Microsoft over the Microsoft 365 breach.
They nail a new detail - one of the 'acquired' signing keys expired in 2021, but apparently it was still valid in Microsoft's cloud services. https://www.wiz.io/blog/storm-0558-compromised-microsoft-key-enables-authentication-of-countless-micr
Compromised Microsoft Key: More Impactful Than We Thought | Wiz Blog
Our investigation of the security incident disclosed by Microsoft and CISA and attributed to Chinese threat actor Storm-0558, found that this incident seems to have a broader scope than originally assumed. Organizations using Microsoft and Azure services should take steps to assess potential impact.
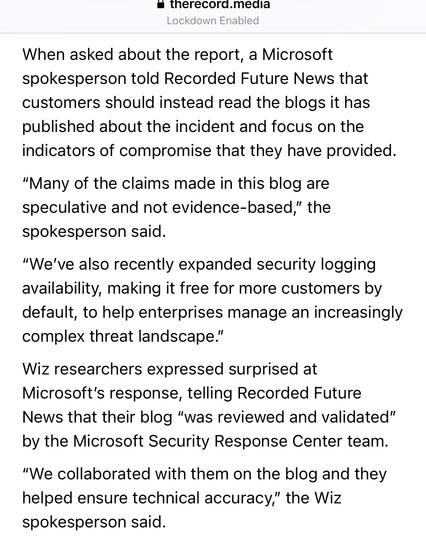
YOU MUST ONLY READ THE OFFICIAL BLOGS
there is no breach
there is no vulnerability
there are no zero days
*jedi wave*
https://therecord.media/microsoft-disputes-report-on-chinese-hacking
The Microsoft write up on how Microsoft 365 got owned to steal customer emails is out. It’s really good and honest from a technical level I think, if you’ve been following the details closely. Top points to the US Gov for forcing public disclosure originally btw.
Preventing Authentication Bypass: A Tale of Two Researchers
There’s a pretty good look at unanswered questions the MSRC blog on the Microsoft 365 customer data breach in this: https://arstechnica.com/security/2023/09/hack-of-a-microsoft-corporate-account-led-to-azure-breach-by-chinese-hackers/
Unsurprisingly MS aren’t using words like ‘breach’, ‘vulnerability’ etc when clearly it was both. It’s almost like there’s misaligned incentives.
Other obvious issues include a compromise in 2021 where the threat actor took process dumps etc but nobody checked what they were doing (you live and learn etc), no HSMs etc. Assume MS are compromised.
This TechCrunch piece has one extra detail not in the MSFT blog on the Microsoft 365 data breach - access was gained via session token theft.
To expand, Microsoft use Azure AD MFA, which has a problem with session token theft. https://techcrunch.com/2023/09/08/microsoft-hacker-china-government-storm-0558/
US State Department have gone on the record about how they found the Microsoft 365 data breach.
They set up a detection rule called Big Yellow Taxi two years ago to look for unknown AppIDs in OfficeActivity, which ultimately saved Microsoft’s ass.
https://www.politico.com/news/2023/09/15/digital-tripwire-helped-state-uncover-chinese-hack-00115973
Chinese hackers stole emails from US State Dept in Microsoft breach, Senate staffer says
Chinese hackers who breached Microsoft's <a href="https://www.reuters.com/markets/companies/MSFT.O" target="_blank">(MSFT.O)</a> email platform this year managed to steal tens of thousands of emails from U.S. State Department accounts, a Senate staffer told Reuters on Wednesday.
Microsoft have announced they are going to start using Azure HSM for their own services finally, after being cyber bullied by GossiTheDog. https://www.microsoft.com/en-us/security/blog/2023/11/02/announcing-microsoft-secure-future-initiative-to-advance-security-engineering/
(It’s actually a really good blog with a bunch of good ideas, if you ignore the AI stuff).
Absolutely blistering independent review into Microsoft 365 breach early last year is due this week from Cyber Safety Review Board, highlights huge problems with Microsoft’s security.
I did not participate.
Contains something I didn’t know - last month, Microsoft quietly corrected a blog to say they never found the crash dump with the certificate, so do not know how China got it. They did not store it in a HSM.
References earlier breach they hadn’t disclosed.
sweet jeebus.... 😬
@Ratanasec @GossiTheDog I would argue that it's not really serious tradecraft -- I'm reading between the lines but it sounds like the compromise was limited to a single engineer's account. They don't go into details but this may have included access to a laptop/desktop ("Ooooo, memory dumps! Let's copy those somewhere") or it might've been e-mail/O365, which may have had sufficient data to access whatever file transfer/sharing platform was being used. Heck, the memory dump might've been stored in OneDrive.
And finding something like this in a memory dump and extracting it isn't particularly difficult, either.
But...my takeaway is that tradecraft usually comes into play in moving laterally and staying resident. Compromises of a single user where the attacker doesn't move around and doesn't stick around often don't create enough noise to get noticed & investigated (or taken very seriously).
@GossiTheDog A friend said something to the effect of "Nothing in the MSRC blog covers hardening the corporate network,I guess that's implied."
My response was:
'I think it's more "We fully expect corpnet to get compromised again and we're not sure we can prevent it, we're going to try harder to keep sensitive info off it."'
The new NSA key in Windows is much better hidden.
What was the timeline provided for when the compromise actually occurred?
heh...
I joked about how they couldnt even afford to store all the logs needed and I have Larry Literals in my DMs and mentions telling me how they cant keep everything due to possible regulations and all...
Like...
Total
LoL.
uhg
The Storm-0588 hack reminds me of the movie Groundhog Day.
https://www.wired.com/story/the-full-story-of-the-stunning-rsa-hack-can-finally-be-told/
@isomer @briankrebs @GossiTheDog i don't like the phasing "due to GDPR" since retention is a nuanced and complicated matter.
But I can't get into too much of that for obvious reasons.
Random cynical thought:
MS dogfoods their own cloud. And since the cloud charges to actually keep the logs, they don't want to pay the internal recharge rate so they don't keep the logs.
@GossiTheDog Kevin, do you think Microsoft should disclose how the corporate account of its engineer got hacked? This seems like an important detail assuming Microsoft's goal is transparency.
Also, what do you think of the repeated use of the word "issue" in the post? Isn't "vulnerability" the correct term here?
So the attackers discovered key material in Microsoft's super secure corporate environment that Microsoft itself didn't know had left the production environment, were able to exfiltrate the key material, and Microsoft doesn't want to have noticed any of this?
That sounds very unbelievable to me.
@doessec @GossiTheDog
My mind was like "Riiiiight 🤫" APT just so happen to compromise an account and miraculously happen to find the proverbial needle in the haystack. And of course the log retention deleted all traces of this.
If I were to write the movie script, I would make it more believable, and put an insider threat in place that, when this person found that key just thought 💰💰💰 jackpot, retirement secured 😎
But, these guys would most likely have had that account compromised a long time and sifted through dumps on a regular basis looking for exactly something like this.
I would... 🤗
Smilyanets and Cimpanu both always provide intriguing content
iTWire - Azure breach: Microsoft okays Wiz post on continued danger, then denies it
Microsoft is continuing to obfuscate about a recent attack on its Azure cloud infrastructure, saying a post, that claims danger from the attack still exists, is speculative and not evidence-based. The company is mentioned in that same post as having checked the content for technical accuracy. Shir T...