They used Outlook Web App - runs the Exchange Server codebase btw - to craft tokens to bypass auth.
There's some clever wording in blog around only impacting OWA. OWA is a part of Microsoft 365 and Exchange Online.
The problem was discovered by the US Government and reported to Microsoft. https://edition.cnn.com/2023/07/12/politics/china-based-hackers-us-government-email-intl-hnk/index.html
This one looks like a huge mistake, a consumer MSA key (managed end to end by Microsoft - there's no external logs) was able to forge any Azure AD key.
It's only become public it appears as the US Government told Microsoft, which forces public disclosure.
CISA's advisory on the Microsoft 365 compromise is wayyyyyyyyyyy better than the Microsoft advisory - contains actionable hunting and logging information. Kinda nuts that the US Government are providing better information about Microsoft than Microsoft.
Okay - I found a victim org.
The situation for them is 😬
MS are going to have to release more info, methinks.. or I crank out the blog writing.
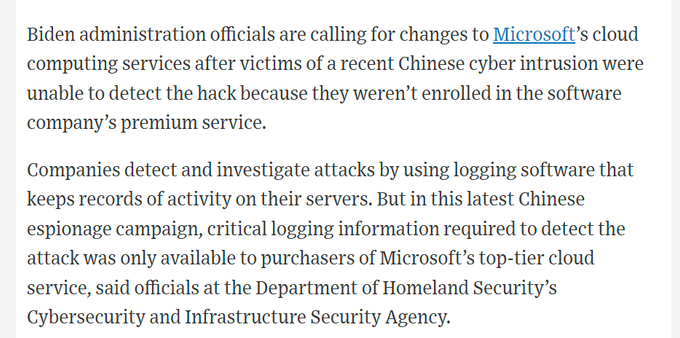
Really good Washington Post piece on the breach of Microsoft 365’s email service.
- hackers accessed customer emails for a month
- Microsoft didn’t notice
- USG had to tell them
- The access to generate tokens very likely came from MS being hacked and not realising
Talked to another impacted victim org in the Microsoft 365 hack, they basically got no actionable info from MS. Basically ‘lol you got hacked’ with wordsmithing and padding. 👀😬
I think I’m going to post hunting queries for this with an MS Paint logo.
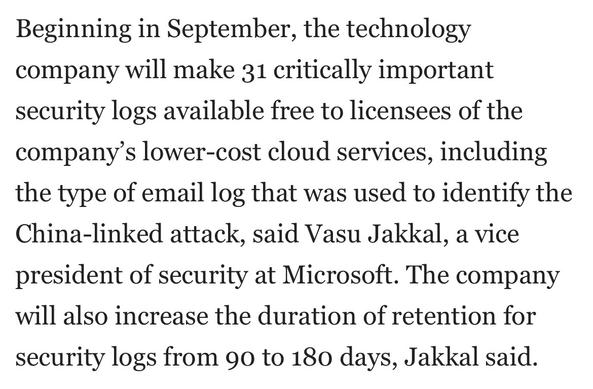
🎶 regulation 🎶
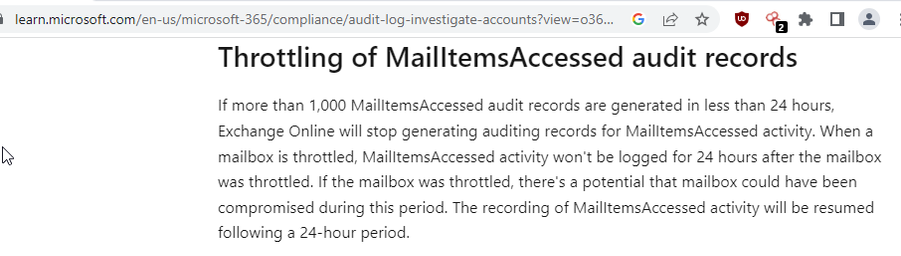
I agree with CISA here (and have publicly for years) - security access logs for customers own services shouldn't be locked behind E5 per user licensing.
Yes, it will cost Microsoft money in upsell. They're more profitable than a large portion of the UK economy; they can afford it.
I should also point out the reason Microsoft was able to tell orgs specifically that they'd be targeted even when they didn't have E5 is MS already store the logs anyway.
“We don’t have any evidence that the actor exploited a 0day." say Microsoft. Their first blog on this says “exploit” - so are MS saying they don’t patch vulnerabilities in their cloud? 🤔
Their latest blog also says “This was made possible by a validation error in Microsoft code” - which is a vulnerability. Which is a 0day as it was under exploitation before Microsoft knew of it existing.
Microsoft lying to media and customers is not a good look.
All it took was Exchange Online in GCC and GCC High getting breached
Non-E5 users to get some security log availability finally.
Nils Goroll (@[email protected])
In the context of the latest #microsoft #breach https://msrc.microsoft.com/blog/2023/07/microsoft-mitigates-china-based-threat-actor-storm-0558-targeting-of-customer-email/ : We run a daily job checking azure jwks from https://login.microsoftonline.com/<AUD>/discovery/v2.0/keys into git. Here's the history of key ids added and removed since 2022-12-05 (- removed, + added): 2023-06-01: -"nOo3ZDrODXEK1jKWhXslHR_KXEg" 2023-06-02: +"nOo3ZDrODXEK1jKWhXslHR_KXEg" 2023-06-03: -"nOo3ZDrODXEK1jKWhXslHR_KXEg" 2023-06-22: -"l3sQ-50cCH4xBVZLHTGwnSR7680" 2023-07-13: -"Mr5-AUibfBii7Nd1jBebaxboXW0" more in 🧵#infosec
Maybe E5 was too expensive and they just don't have logs.
@GossiTheDog @dangoodin did we know this little tidbit before?
"Though the key was intended only for MSA accounts, a validation issue allowed this key to be trusted for signing Azure AD tokens. This issue has been corrected."
@dangoodin I don't think Microsoft ever acknowledges vulnerabilities in their cloud services (also there's no CVEs for cloud), and you don't say breach at Microsoft.
So if you Ctrl+F I doubt you will find vulnerability or breach in relation to Microsoft.
They did say "exploit" in the original MSRC blog in relation to Microsoft's cloud services, and you exploit a vulnerability. So I think it's fair to say that, yes, they had vuln(s).
#gdpr basic rights for customers.
@GossiTheDog given how much Azure fraud is a result of credential stuffing, I’ve long argued that MSFT might very well save money by taking the account protection features currently gated by E3/E5/AAD P1/P2 and making them free for everyone.
Even if they didn’t save money on that, like you said: they could afford it.
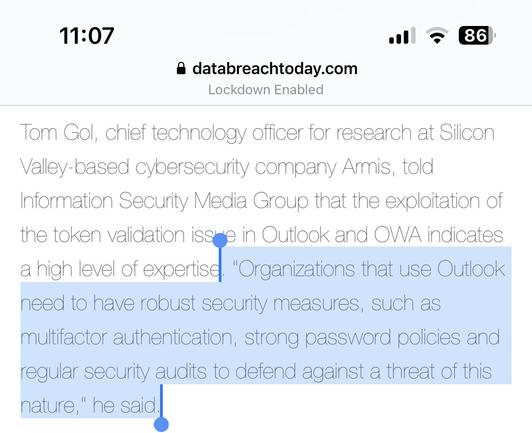
Wherein "robust security measures" means mark Microsoft as untrusted.
@GossiTheDog the blog says
"Our telemetry indicates that we have successfully blocked Storm-0558 from accessing customer email using forged authentication tokens."
That surely does not say that they have blocked all the attempts before they blocked them...




 🇨🇦
🇨🇦

