The ESP32 Has Quietly Become One of the Most Interesting Hacker Devices Alive
Expensive hardware often becomes ornamental. People baby it. They curate it. They build identities around owning it. Cheap hardware gets modified until it resembles evidence recovered from a flooded basement.Want your brand in front of 1000s of RF engineers, SDR enthusiasts, and wireless security researchers?
RF Hackers Sanctuary is open for 2026 sponsors.
Your gear.
Their hands.
Real signal.
https://rfhackers.com/sponsors/
#SDR #RFHacking #WirelessSecurity #HamRadio
Passive RF sensing is becoming real.
Open-source π RuView uses WiFi CSI data and low-cost ESP32 microcontroller nodes to reconstruct human body pose through walls.
Inspired by research from Carnegie Mellon University.
New physical-layer surveillance risk?
Source: https://cybersecuritynews.com/wifi-signals-reveal-human-activities/
Follow TechNadu for infosec insights.
🎁 Holiday Giveaway🎁
Sponsored by Suzu Labs, the Phillip Wylie Show is giving away a HAK5 WiFi Pineapple Pager — a powerful tool for wireless security assessments and red team operations.
👉 Enter here: https://suzulabs.com/giveaway
Huge thanks to Suzu Labs for supporting the cybersecurity community.
#Cybersecurity #OffensiveSecurity #PenTesting #WirelessSecurity #Giveaway
Enhance Safety with Wireless Security Camera Systems Dubai
VRS Technologies LLC provides top-grade Wireless Security Camera Systems Dubai for homes and businesses. Our advanced wireless CCTV solutions ensure seamless monitoring, reliability, and easy installation. For expert setup and support, contact us at +971505319306.
Visit Us: https://www.cctvinstallationdubai.ae/services/wireless-security-camera-systems-dubai-uae/
#wirelesscctv #securitycameras #cctvuae #dubaisecurity #cctvinstallation #surveillance #vrtstechnologiesllc #wirelesssecurity
Auch 2026 findet wieder ein #GI-SPRING-Graduiertenworkshop der Fachgruppe Security - Intrusion Detection and Response (SIDAR) statt. Diesmal am 21. und 22.04.2026 in #Heidelberg.
Zu den Themen gehören #VulnerabilityAssessment, #ThreatIntelligence, #IntrusionDetection, #Malware, #IncidentManagement, #WirelessSecurity, #DigitalForensics usw.
Einreichungen werden bis zum 15.03.2026 angenommen.
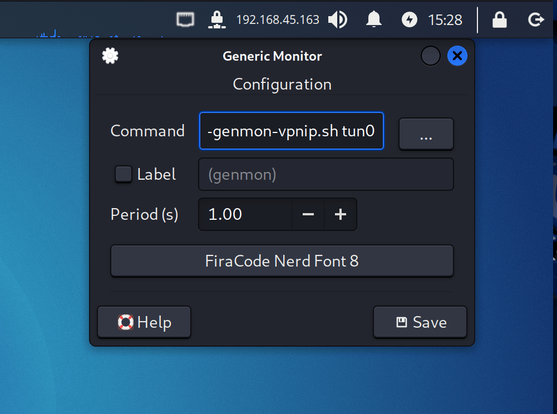
🐉 Kali Linux 2025.3 Release — Vagrant, Nexmon & NetHunter Love 🚀
Kali 2025.3 just dropped with a tidy set of quality-of-life updates and some neat platform improvements. The team refreshed how they build Vagrant images (moving the VM workflow away from Packer towards a cleaner build pipeline), making virtual images easier to manage for labs and CI. 🧩🖥️
A big win for wireless researchers: Nexmon support returns (Broadcom/Cypress chips), bringing monitor mode and injection support back to devices including Raspberry Pi models (now supporting Pi 5). That means more accessible packet capture and radio experiments on compact SBCs. 📡🐧
Kali is also trimming legacy support — dropping ARMel — and polishing desktop niceties like a configurable Xfce VPN-IP panel so multi-VPN users can choose which interface to show. 🌐🔧
New tools (10) were added to the repos — highlights include Caido, Detect It Easy (DiE), krbrelayx, ligolo-mp, llm-tools-nmap, and patchleaks — plus many package updates. Expect easier reverse/forensics workflows, Kerberos tooling, AI-cli helpers, and utilities to speed up patch validation. 🧰✨
Kali NetHunter also got attention: a Nexmon-enabled Samsung Galaxy S10 image (budget-friendly internal monitor + injection), CARsenal (car-hacking toolkit) updates and refactors, Magisk module support for kernel modules (experimental), and a raft of bug fixes/UI work for mobile tooling. 📱⚙️
ARM builds were refined (recommend arm64 Raspberry Pi images, Pi 5 support, kernel update fixes) and there are the usual documentation updates, community wallpapers, and repository tweaks. If you run Kali in lab or mobile setups, this release is worth testing. 🔁📚
⚠️ Disclaimer:
For educational & authorized use only. Kali’s wireless/attack-capability features (monitor/injection, CARsenal, NetHunter) must be used responsibly in controlled labs or with explicit permission.
#KaliLinux #Kali2025 #NetHunter #Nexmon #Infosec #PenTesting #WirelessSecurity #CyberSecurity #InfoSec
This summer, our researcher Nikola Antonijević attended #WiSec2025 & wrote a blog post on "Security in the Inaudible World" – challenges in inaudible communication 👇
🔗 https://www.esat.kuleuven.be/cosic/blog/wisec-2025-spotlight-security-in-the-inaudible-world/
Nikola also presented "ZeroTouch" at #SACMAT2025, reinforcing RSS for secure geofencing 👇 https://www.esat.kuleuven.be/cosic/blog/zerotouch-reinforcing-rss-for-secure-geofencing/
#WirelessSecurity #Geofencing
Wireless Security Protocols Explained: WEP, WPA, WPA2 & WPA3 📡🔐
Understanding wireless security protocols is essential for protecting your network from unauthorized access and ensuring data confidentiality.
📘 Key Protocols & Their Characteristics:
1. WEP (Wired Equivalent Privacy)
• Introduced in 1997
• Weak encryption (RC4), easily cracked
• Deprecated and insecure
2. WPA (Wi-Fi Protected Access)
• Interim solution after WEP
• Improved encryption with TKIP
• Still vulnerable to certain attacks
3. WPA2
• Widely used today
• Uses AES-based CCMP encryption
• Supports enterprise (RADIUS) and personal (PSK) modes
4. WPA3
• Latest standard with stronger security
• Resistant to brute-force attacks
• Supports SAE (Simultaneous Authentication of Equals)
• Enhanced encryption and forward secrecy
Why it matters:
Choosing the right wireless protocol significantly affects your network’s resilience against common attack vectors such as packet sniffing, replay attacks, and credential theft.
Disclaimer: This post is for educational and awareness purposes only. Always secure your wireless networks using the latest standards.
#WirelessSecurity #WPA3 #WEP #WPA2 #CyberSecurity #InfoSec #EducationOnly #WiFiProtocols #NetworkSecurity #WiFiEncryption