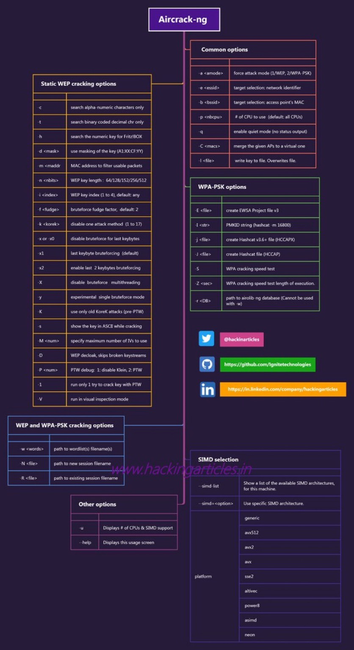
Wireless Penetration Testing Tools You Should Know 📡🔐
Wireless networks can be a critical attack surface if not properly secured. These tools are widely used in authorized lab environments to assess the strength of Wi-Fi configurations and encryption protocols.
Use cases include:
• Testing weak encryption (WEP/WPA)
• Detecting rogue access points
• Capturing and analyzing authentication handshakes
• Teaching wireless attack vectors in controlled labs
Disclaimer: This content is for educational and ethical use only. Wireless testing must only be performed on networks you own or have explicit authorization to audit.
#WirelessSecurity #WiFiPentest #CyberSecurity #InfoSec #EthicalHacking #EducationOnly #RedTeamTools #WirelessAuditing #AircrackNG #WPA2