Check out ˗ˏˋ ⭒ https://lnkd.in/gE2wUqgc ⭒ ˎˊ˗ to see my intro whilst you listen.
I'm thus re-naming this work as "CVE Keeper - Security at x+1; rethinking vulnerability management beyond CVSS & scanners". I must also thank @andrewpollock for reviewing several of my verbose drafts. 🫡
So, Security at x+1; rethinking vulnerability management beyond CVSS & scanners -
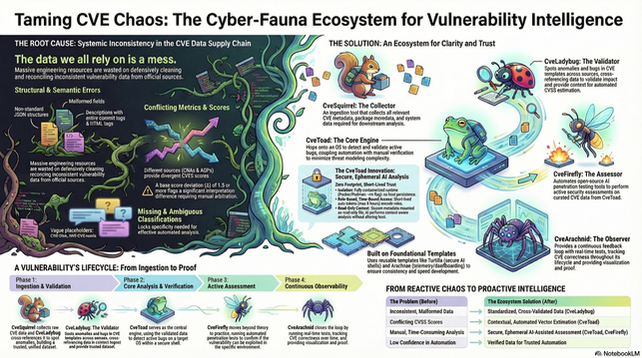
Most vulnerability tooling today is optimized for disclosure and alert volume, not for making correct decisions on real systems. CVEs arrive faster than teams can evaluate them, scores are generic, context arrives late, and we still struggle to answer the only question that matters: does this actually put my system at risk right now?
Over the last few years working close to CVE lifecycle automation, I’ve been designing an open architecture that treats vulnerability management as a continuous, system-specific reasoning problem rather than a static scoring task. The goal is to assess impact on the same day for 0-days using minimal upstream data, refine accuracy over time as context improves, reason across dependencies and compound vulnerabilities, and couple automation with explicit human verification instead of replacing it.
This work explores:
⤇ 1• Same-day triage of newly disclosed and 0-day vulnerabilities
⤇ 2• Dependency-aware and compound vulnerability impact assessment
⤇ 3• Correlating classical CVSS with AI-specific threat vectors
⤇ 4• Reducing operational noise, unnecessary reboots, and security burnout
⤇ 5• Making high-quality vulnerability intelligence accessible beyond enterprise teams
The core belief is simple: most security failures come from misjudged impact, not missed vulnerabilities. Accuracy, context, and accountability matter more than volume.
I’m sharing this to invite feedback from folks working in CVE, OSV, vulnerability disclosure, AI security, infra, and systems research. Disagreement and critique are welcome. This problem affects everyone, and I don’t think incremental tooling alone will solve it.
P.S.
- Super appreciate everyone that's spent time reviewing my drafts and reading all my essays lol. I owe you 🫶🏻
- ... and GoogleLM. These slides would have taken me forever to make otherwise.
Take my CVE-data User Survey to allow me to tailor your needs into my design - lnkd.in/gcyvnZeE
See more at - lnkd.in/gGWQfBW5
lnkd.in/gE2wUqgc
#VulnerabilityManagement #Risk #ThreatModeling #CVE #CyberSecurity #Infosec #VulnerabilityManagement #ThreatIntelligence #ApplicationSecurity #SecurityOperations #ZeroDay #RiskManagement #DevSecOps #CVE #CVEAnalysis #VulnerabilityDisclosure #SecurityData #CVSS #VulnerabilityAssessment #PatchManagement #AI #AIML #AISecurity #MachineLearning #AIThreats #AIinSecurity #SecureAI #OSS #Rust #ZeroTrust #Security
https://www.linkedin.com/feed/update/urn:li:activity:7409399623087370240