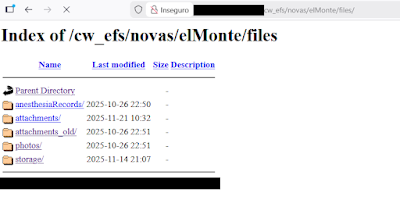
Responsible Disclosure is a cornerstone of cybersecurity. Without it, we allow malicious actors to have a head start compared to the developers who aim to fix the identified vulnerabilities. Therefore, I find it worrying that Microsoft now has to put out an announcement to stick to these best practices.
There might be cases where public disclosure is better than waiting for a fix. If an organization refuse to acknowledge a problem, for example. But even then, they need to be given reasonable time to respond to the findings/reports.
At worst, innocent bystanders (such as customers) might be negatively impacted (e.g., through leakage of private information) because of the recklessness of some "security researchers", who might have had good intentions.
Microsofts announcement: https://www.microsoft.com/en-us/msrc/blog/2026/05/a-shared-responsibility-protecting-customers-through-coordinated-vulnerability-disclosure
#cybersecurity #security #infosec #vulnerability #responsibledisclosure #microsoft