Major Upgrade on UPX:
Upakowane ELFy – czerwona flaga dla pliku binarnego w Linuksie ( https://nfsec.pl/security/6600 ) #linux #malware #upx #packer #security #twittermigration
NF.sec – Bezpieczeństwo systemu Linux - Upakowane ELFy – czerwona flaga dla pliku binarnego w Linuksie
U ltimate Packer for Executables (UPX) to program pakujący dla kilku formatów wykonywalnych, takich jak biblioteki DLL systemu Windows, aplikacji macOS oraz Linux ELF. Jak możemy przeczytać na oficjalnej stronie programu UPX: “potrafi zazwyczaj zmniejszyć rozmiar plików programów i bibliotek DDL o około 50% – 70%, redukując w ten sposób miejsce na dysku, czas ładowania […]
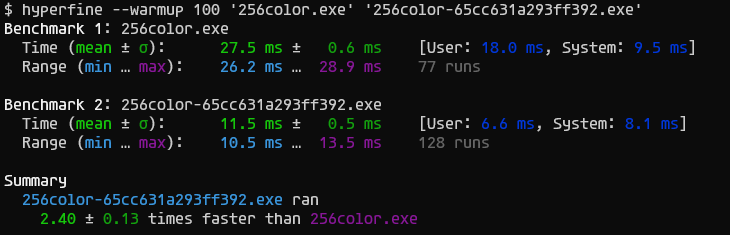
@RL_Dane Oh, compressing executables still makes sense in *some* scenarios (relevant size reduction, not using a filesystem with transparent compression, "slow" storage media ...).
But then, #gzexe doesn't really cut it. It needs temporary files for decompression (spoiling most possible speed gains), and compression rates are mediocre. So *if* you have a use case for compressed executables, you'd better have a look at #upx, which achieves better rates and decompresses in-memory, in-place.
Heap Buffer Overflow in UPX Identified
Date: March 26, 2024
CVE: To be assigned
Vulnerability Type: Buffer Errors
CWE: [[CWE-122]]
Sources: NIST VULNDB VULNDB Submit
Issue Summary
A heap buffer overflow vulnerability was identified in the [[UPX|Ultimate Packer for eXecutables]] (UPX), specifically in the commit 06b0de9c77551cd4e856d453e094d8a0b6ef0d6d. This issue occurs during the handling of certain data structures, leading to potential memory corruption. The vulnerability was discovered through fuzzing techniques using the Google OSS-Fuzz project.
Technical Key findings
The vulnerability is caused by improper handling of input data, resulting in a heap buffer overflow. This overflow occurs in the handling of packed files during decompression, where the bounds of allocated heap memory are not properly checked.
Vulnerable products
- [[UPX]] version identified by commit
06b0de9c77551cd4e856d453e094d8a0b6ef0d6d.
Impact assessment
An attacker could exploit this vulnerability to execute arbitrary code on the target system or cause a denial of service through application crash, potentially compromising the system's integrity and availability.
Patches or workaround
No specific patches or workarounds were mentioned at the time of reporting. Users are advised to monitor the official [[UPX]] GitHub repository for updates.
Tags
#UPX #BufferOverflow #HeapOverflow #SecurityVulnerability #CVE