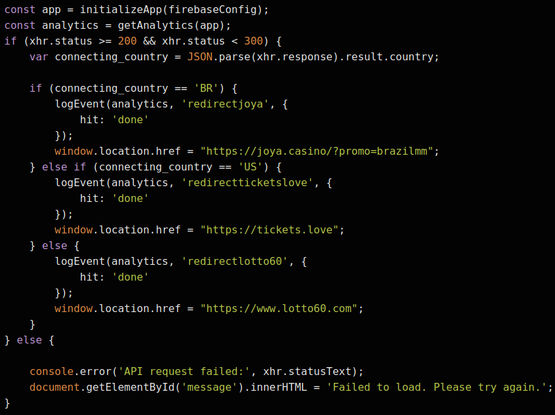
Threat actor using lookalike domains that drive through a traffic distribution system (TDS) to illegal gambling and malicious content. This actor runs a TDS using a few different domains, including choto[.]xyz and choto[.]click. The attack chain typically begins when an internet user unknowingly mistypes a website (e.g. dizscord[.]com instead of discord.com). Subsequently, the user is profiled via one or two TDS servers and then conditionally redirected to a fraudulent webpage. Earlier this year, they ran campaigns that leveraged a second stage TDS (victory-leads[.]xyz) that conditionally routed users to different malicious content based on their geo-location (see attached image). We recommend blocking the following TDS domains; doing so will effectively disrupt the attack chains that are conducted by this actor. Currently, only choto[.]click appears to be actively used. We have been tracking this TDS since Spring 2023.
<Lookalike Domains>
donga[.]delivery (imitating donga.com - South Korean newspaper company)
tutorialspoint[.]pics (imitating tutorialspoint.com - video tutorial education service)
icicibank[.]observer (imitating icicibank.com - Indian banking)
netflixg[.]com (imitating netflix.com - video streaming service)
capktalone[.]com (imitating capitalone.com - American banking company)
cbssportas[.]com (imitating cbssports.com - American sports network)
betwah[.]de (imitating betway.com - British gambling company)
<TDS Domains>
choto[.]click
choto[.]xyz
choto[.]store
victory-leads[.]xyz
<Fraud Landing Page Domains>
lotto60[.]com
joya[.]casino
tickets[.]love
#dns #cybersecurity #InfobloxThreatIntel #Infoblox #tds #gambling #scam #lookalike #typosquat #threatintel #cybercrime