----------------
🛠️ Tool: Pcap2Timeline - Fast PCAP triage into analyst-friendly CSV output
===================
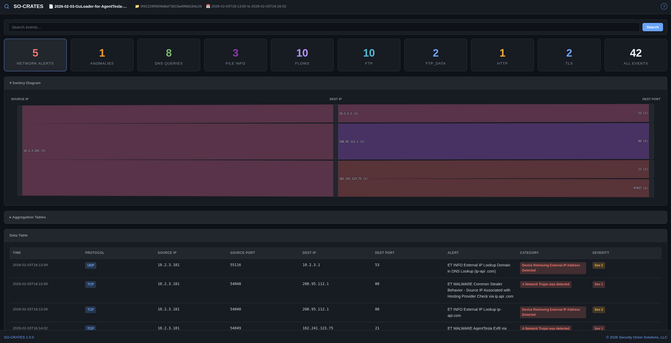
Pcap2Timeline is a lightweight shell script (pcap2csv.sh) that wraps Suricata to transform raw PCAP files into structured CSV datasets. It leverages Suricata's eve.json output and converts it into multiple CSV files, one per event type, plus a chronologically merged timeline.
🔹 Key Features
The script extracts the following event categories from PCAP files:
• Alerts - Suricata rule match notifications
• DNS - Queries and responses
• HTTP - Request and response metadata
• TLS - SNI, certificate information
• FTP - Commands and file transfers
• SMB - Windows file sharing activity
• SSH - Secure shell sessions
• RDP - Remote desktop connections
• Flows - Connection statistics and metadata
Each event type gets its own CSV, and a combined capture_timeline.csv merges all events in chronological order. Custom Suricata rules can be applied via the -R flag, enabling targeted detection during triage instead of relying only on default rule sets.
🔹 Technical Implementation
The script is written in POSIX sh with no bashisms, meaning it runs on minimal Unix environments without requiring bash. Dependencies are intentionally sparse: suricata for packet processing and jq for JSON parsing. Standard POSIX utilities handle the rest.
Given an input capture.pcap, the script creates a pcap2csv_output/ directory containing separate CSVs for alerts, DNS, HTTP, TLS, FTP, flows, and the merged timeline.
This integrates cleanly with Eric Zimmerman's Timeline Explorer for interactive filtering and pivoting through the results.
🔹 Setup
sudo apt install suricata jq
sudo suricata-update
git clone https://github.com/mf1d3l/Pcap2Timeline.git
chmod +x pcap2csv.sh
Usage: ./pcap2csv.sh <input.pcap> [-R <rules-file.rules>]
🔹 Considerations
The tool fills a specific niche: rapid initial triage, not deep analysis. It does not correlate events across categories or generate findings automatically. Analysts still need to interpret the data, but having it pre-organized by event type with a unified timeline significantly reduces orientation time within a new PCAP. The extraction is bounded by what Suricata can detect, so protocols not covered by the loaded rule set will not appear in output.
🔹 tool #PCAP #Suricata #DFIR #networkforensics
🔗 Source: https://github.com/mf1d3l/Pcap2Timeline