My homelab is now using NRPE with TLS thanks to the private PKI I deployed this week-end.
Achievement unlocked 🔓
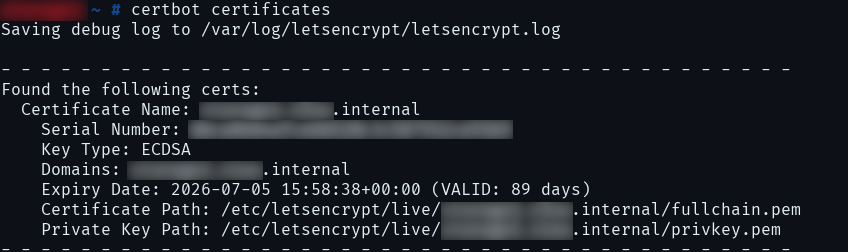
My homelab has now valid internal TLS certificates automatically renewed by certbot on a step-ca server.
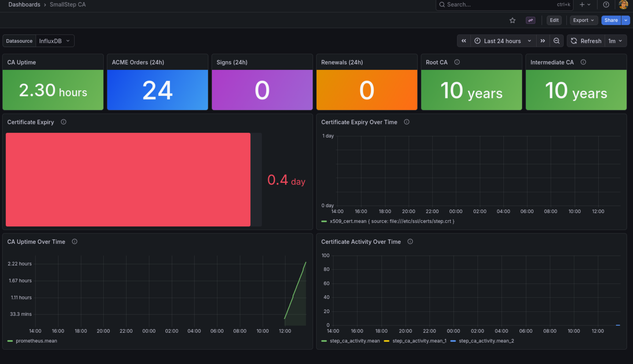
Step CA configured with PostgreSQL backend and the ACME provider in my homelab. Clients trust the CA. Next steps: configure certbot and add monitoring to check certificates expiration.
#homelab #selhosting #stepca

Be the LetsEncrypt in your homelab with step-ca
So you have a Cute Homelab and you want to use it to secure your services and containers with x509 certificates? But your homelab isn’t on the internet, so you can’t simply use LetsEncrypt? Well. You can become your own LetsEncrypt and hand out certificates with certbot. You “just” need to run your own CA (Certificate Authority). Sounds frightening and complicated? It kinda is, but not really when you use step-ca, an open source solution that you can run in a container.
Es war am Ende eine härtere Nuss, als gedacht, aber mein Heimnetz hat jetzt eine eigene CA auf Basis von #stepca , #caddy läuft als Reverse Proxy und wickelt das Zertifikatshandling automatisiert für die im #homelab laufenden Dienste ab.
Eine Grundlage, die ich schon länger habe wollte, aber mir nie die Zeit genommen habe, tiefer einzusteigen und das einmal ordentlich aufzusetzen.
Next up: Backups machen und dokumentieren, was ich getan hab.
@Larvitz How is Step CA? Are you coming from another CA solution?
Been thinking about running #stepca in my #kubernetes cluster, but have been apprehensive because of how many features seem to be gated behind smallstep's proprietary version. Would love to have this integrated with #certmanager and using the #tpm on my nodes. Was going to do a rearchitecting of my entire #auth and #cryptography stack when I switch from the deprecated #Ingress API to the #GatewayAPI