Is your Ubuntu Server properly secured? Our 2026 guide covers 7 essential hardening steps including SSH security, UFW firewall, Fail2Ban, and automated patches. Essential reading for system administrators! #UbuntuServer #ServerSecurity #LinuxAdmin #ServerHardening #SysAdmin https://estoreab.com/ubuntu-server-security-guide
CPanel's Black Week: 3 New Vulnerabilities Patched After Attack on 44k Servers
#HackerNews #CPanel #Vulnerabilities #BlackWeek #Cybersecurity #Ransomware #ServerSecurity
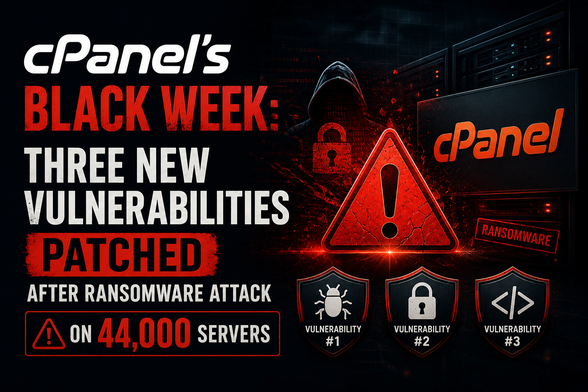
cPanel's Black Week: Three New Vulnerabilities Patched After Ransomware Attack on 44,000 Servers - Copahost
If you run a server with cPanel or WHM, you need to read this carefully. On May 8, 2026 — just ten days after the cPanel CVE-2026-41940 authentication bypass was used to compromise 44,000 web hosting servers and deploy ransomware — cPanel quietly released a second emergency security patch. This one covers three new vulnerabilities: […]
🔴 Hackers Are Inside Your Server Right Now
Someone just walked into your server. No password. No invite. Just in.
https://www.youtube.com/shorts/U8j6QZVslgE
#cybersecurity #cPanel #serversecurity #infosec #ethicalhacking #hacking #cve #vulnerability #threatintel #security
Hackers Are Inside Your Server Right Now #Shorts
Sicherheitslücke in cPanel: So schützt du deinen Webserver vor CVE-2026-41940
#technews #cybersecurity #sysadmin #cpanel #serversecurity #webhosting
cPanel Discloses Authentication Flaw, Urges Immediate Server Updates
cPanel has uncovered a critical authentication flaw that could let hackers gain unauthorized access to your control panel, and is urging immediate server updates to protect against this threat. Check if your version is vulnerable and update to a patched build right away.
#Cpanel #AuthenticationFlaw #ServerSecurity #ControlPanelExploit #EmergingThreats
https://phys.org/news/2026-04-deep-antarctic-ice-cosmic-strange.html #cosmicwhispers #Antarctica400BadRequest #serversecurity #cosmicirony #mutedscream #HackerNews #ngated

Deep under Antarctic ice, a long-predicted cosmic whisper finally breaks through in 13 strange bursts
A detector buried deep in Antarctic ice has captured the first experimental evidence of a predicted but never-before-seen phenomenon: radio pulses generated when high-energy cosmic rays slam into the ice sheet and trigger particle cascades inside it. Through results published in Physical Review Letters, astronomers of the Askaryan Radio Array (ARA) Collaboration have validated a key technique, which they hope will eventually allow them to detect some of the rarest and most energetic particles in the universe.
Apache ActiveMQ Vulnerability Exploited, Hits 6,400 Servers
More than 6,400 publicly accessible Apache ActiveMQ servers are under attack, thanks to a high-severity code injection vulnerability that's being actively exploited. Is your server among them?
#ApacheActivemq #CodeInjection #VulnerabilityExploitation #EmergingThreats #ServerSecurity
Physical Security Lapses Expose Sensitive Servers
Your cybersecurity is only as strong as the physical locks on your servers - and a recent case where a server-room lock proved laughably easy to bypass is a stark reminder of this often-overlooked vulnerability. Leaving sensitive servers exposed is like leaving a car with cash in the console unlocked - it's an open invitation…
#PhysicalSecurity #ServerSecurity #Cybersecurity #EmergingThreats #VulnerabilityManagement
What is Port Knocking Implementation and Security: A Comprehensive Guide
https://denizhalil.com/2026/04/06/port-knocking-implementation-security-guide
#CyberSecurity #PortKnocking #NetworkSecurity #DefenseInDepth #LinuxSecurity #ServerSecurity

What is Port Knocking Implementation and Security: A Comprehensive Guide - DenizHalil - Professional Cybersecurity Consulting and Penetration Testing
Learn everything about port knocking implementation, security risks, attack and defense strategies, and best practices. This comprehensive guide covers how port knocking protects your network and how to deploy it securely against modern threats.
https://jpmens.net/2026/04/03/ssh-certificates-the-better-ssh-experience/ #ServerSecurity #VIPPass #Cybersecurity #TechHumor #HackerNews #ngated




