Reloaded in a modern Remcos RAT Infection
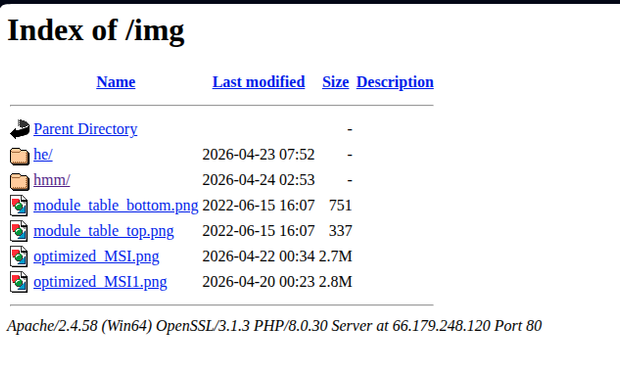
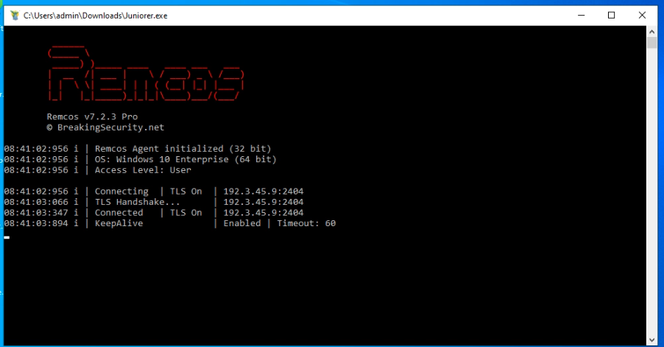
Analysts discovered a new Remcos RAT infection chain starting with a batch file executing encoded commands that creates hidden directories and retrieves encrypted payloads. Unlike earlier campaigns relying on PowerShell-hosted .NET loaders, this variant incorporates DonutLoader shellcode and AutoIt-based staging for in-memory payload delivery. The infection begins with a phishing email containing a malicious batch file named Bestellung.CMD. The chain abuses legitimate Windows utilities including cscript.exe and SyncAppvPublishingServer.vbs to execute Base64-encoded payloads. Additional components are downloaded from cloud storage, including 7Zip tools and password-protected archives containing obfuscated JScript. The final payload consists of DonutLoader shellcode that injects Remcos RAT version 7.2.1 Pro into colorcpl.exe, enabling remote control, credential harvesting, keystroke logging, and additional payload deployment.
Pulse ID: 6a1a2dd905d9f8c4474cb45e
Pulse Link: https://otx.alienvault.com/pulse/6a1a2dd905d9f8c4474cb45e
Pulse Author: AlienVault
Created: 2026-05-30 00:22:49
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#7Zip #Autoit #Cloud #CredentialHarvesting #CyberSecurity #Email #InfoSec #NET #OTX #OpenThreatExchange #Password #Phishing #PowerShell #RAT #Remcos #RemcosRAT #ShellCode #VBS #Windows #Word #ZIP #bot #AlienVault