🚨 𝗣𝗵𝗶𝘀𝗵𝗶𝗻𝗴 𝘃𝗶𝗮 𝗚𝗼𝗼𝗴𝗹𝗲 𝗦𝘁𝗼𝗿𝗮𝗴𝗲 𝗔𝗯𝘂𝘀𝗲 𝗟𝗲𝗮𝗱𝗶𝗻𝗴 𝘁𝗼 𝗥𝗔𝗧 𝗗𝗲𝗽𝗹𝗼𝘆𝗺𝗲𝗻𝘁: 𝗗𝗲𝘁𝗲𝗰𝘁 𝗜𝘁 𝗘𝗮𝗿𝗹𝘆
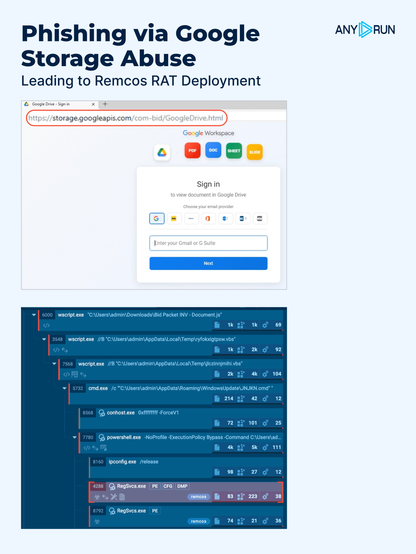
We identified a multi-stage #phishing campaign using a Google Drive-themed lure and delivering #Remcos RAT. Attackers place the HTML on storage[.]googleapis[.]com, abusing trusted infrastructure instead of hosting the phishing page on a newly registered domain.
❗️ 𝗧𝗵𝗲 𝗰𝗵𝗮𝗶𝗻 𝗹𝗲𝘃𝗲𝗿𝗮𝗴𝗲𝘀 𝗥𝗲𝗴𝗦𝘃𝗰𝘀.𝗲𝘅𝗲, 𝗮 𝗹𝗲𝗴𝗶𝘁𝗶𝗺𝗮𝘁𝗲 𝘀𝗶𝗴𝗻𝗲𝗱 𝗠𝗶𝗰𝗿𝗼𝘀𝗼𝗳𝘁/.𝗡𝗘𝗧 𝗯𝗶𝗻𝗮𝗿𝘆 𝘄𝗶𝘁𝗵 𝗮 𝗰𝗹𝗲𝗮𝗻 𝗩𝗶𝗿𝘂𝘀𝗧𝗼𝘁𝗮𝗹 𝗵𝗮𝘀𝗵. Combined with trusted hosting, this makes reputation-based detection unreliable and lowers alert priority during triage. File reputation alone is not enough. Detection depends on behavioral analysis and sandboxing.
⚠️ The page mimics a Google Drive login form, collecting email, password, and OTP. After a “successful login,” the victim is prompted to download Bid-Packet-INV-Document.js, triggering a multi-stage delivery chain:
JS (WSH launcher + time-based evasion) ➡️ VBS Stage 1 (download + hidden execution) ➡️ VBS Stage 2 (%APPDATA%\WindowsUpdate + Startup persistence) ➡️ DYHVQ.ps1 (loader orchestration) ➡️ ZIFDG.tmp (obfuscated PE / Remcos payload) ➡️ Textbin-hosted obfuscated .NET loader (in-memory via Assembly.Load) ➡️ %TEMP%\RegSvcs.exe hollowing/injection ➡️ Partially fileless Remcos + C2 🚨
👨💻 See the analysis session and collect #IOCs to speed up detection and response: https://app.any.run/tasks/0efd1390-c17a-49ce-baef-44b5bd9c4a97/?utm_source=mastodon&utm_medium=post&utm_campaign=google_storage_abuse_phishing&utm_term=080426&utm_content=linktoservice
🔍 Use this TI Lookup query to pivot from IOCs, review related activity, and validate your detection coverage: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=google_storage_abuse_phishing&utm_content=linktotilookup&utm_term=08042026#%7B%22query%22:%22domainName:%5C%22www.freepnglogos.com%5C%22%20and%20domainName:%5C%22storage.googleapis.com%5C%22%20and%20threatLevel:%5C%22malicious%5C%22%22,%22dateRange%22:30%7D
⚡️ Equip your SOC with stronger phishing detection and contain incidents faster: https://any.run/phishing/?utm_source=mastodon&utm_medium=post&utm_campaign=google_storage_abuse_phishing&utm_term=080426&utm_content=linktophishingpage