Hey #redteamer #pentester
What kind of vulnerability you call when a contact form that should have a locked destination email, doesn't, and you can send and email for anyone? (practical effect was, we could send an email originating from an oficial address and that was send from the official server, so, ultra low chance of being marked as spam)
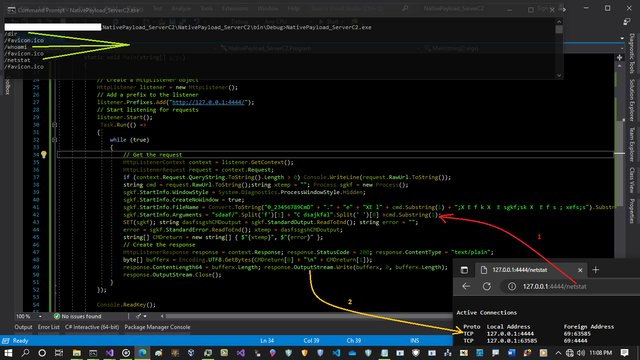
some little bit codes added to my Blue team code to detect some opcodes in injected bytes (especially for this DripLoader or something like this code)
this update version still needs some codes to be better but i working on this hard ;D , just for test some codes in Driploader.cpp was changed by me only for test ;)
i Tested old Loader called "#DripLoader" , and this will bypass ETW events but my blue team tool not fully bypassed and code was detected...
background of this code is really nice and i working on this so maybe you want to see what happened in my test about this as #pentester or #Redteamer this will help you to better understanding ETW or other #eventbased #detections .
as #blueteamer you can see this with this method sometimes your tools will confuse very simple ;p in these pictures you can see startaddress via ETW was not Detected correctly.
Note: it does not mean that sartaddress is fake, i just want to say that startaddress 0x7ffca90... is not about shell code which started with bytes {0xb8 , 0x00 , 0x00 , 0xdd, 0xdd},its about jmp,Mov/BaseAddress/0xdddd0000 & you can find that bytes in C++ source code of driploader:
line 12 of DripLoader.cpp
unsigned char jmpSc[7] {0xB8,b[0],b[1],b[2],b[3],0xFF,0xE0};
worth to read =>
more detail about background of code: https://lnkd.in/ekpHUBsv
this code was added to my list long time ago => https://lnkd.in/eeStM9C
#blueteam #tools #redteam #pentesting #avs #edr #socanalyst #soc
#etw #threadinjection #threathunting #threatdetection
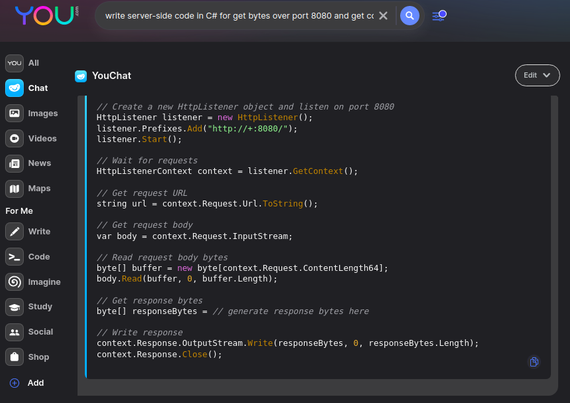
#chatgpt #youdotcom #learning #blueteam #redteam #pentesting #securityresearch #defensive #ai #video #c2 #csharp #inmemory #redteam #pentest
now i want to share something for red-teaming via "Chatgpt" or "YOUdotCOM" as Security Researcher you can see with very simple trick you can find very useful codes here "YOU.COM" which is useful for #pentester or #redteamer , in this case i searched this "write server-side code in C# for/to get bytes over port 8080 and get context" or something like that , and i had this result by #AI so with little bit changing code i made my very simple Sever-Side #C2 only with (50-60 lines server side code), as you can see with very simple code via "Chatgpt" or you-dot-com you can make your own simple C2 Server core codes (networking) or ...
New Video for New codes, this Project is more than 60 lines ;D
Video: Simple C2 server by C# , "Using Chat + AI for C2 Network Core codes and ... make this simple C2 server in [1 hour] with AI help"
in last post i talked about blue-teaming, now i want to share something for red-teaming via "Chatgpt" or "YOUdotCOM" as Security Researcher you can see with very simple trick you can find very useful codes here "YOU.COM" which is useful for #pentester or #redteamer , in this case i searched this "write server-side code in C# for/to get bytes over port 8080 and get context" or something like that , and i had this result by #AI so with little bit changing code i made my very simple Sever-Side C2 only with (50-60 lines server side code), as you can see with very simple code via "Chatgpt" or you-dot-com you can make your own simple C2 Server core codes (networking) or ... but in this case my code executed in server side but i can change that then instead server side my CMD will run in Client-side & vice versa ;D, so as #Penester / #Redteamer and #blueteamer this will help you a lot , also this will be useful for Cyber security Instructors to learn new things better/faster also teaching them better etc
i wrote this code only in 10 mins , because i created my own C2 server with some techniques like this in C# but my core code in background worked with Async Methods and this code almost is similar to my core codes in my own C2 which i created 2-3 months ago so i made this code very fast because i had experience for working with them, but probably for you, this will take time more than 10 mins ;), maybe not, anyway as you can see for learning cyber security things , these platforms are awesome so this one was simple Example for Red-teaming
those Cyber Security guys which called itself #pentester or #Redteamer or #SecurityResearcher "just because" they are in university (learning something As [basics ;D more often] or academic things or out-of-date things ;D) and they "did not have any Experience" in Cyber Security Fields (even 1 year) and some of them even did not have any good/unique/new Cyber Security Research or tools/codes (which shared before to public).
and yeah we call them beginner "geniuses" in cyber security lol
Vs
those Cyber Security Guys which they have at least 3-5 years experience of learning real/new/unique things in these fields like #penetrationtesting or #redteaming or #securityresearch .
believe me your academic things are "Bullshit" and your instructors did not have updated content , they even don't have good viewpoint for cyber security fields like Penetration test or ... ,more often they don't have any experience of working with Offensive tools like Modern C2 servers, they don't know how you can write Offensive Codes like Writing #C2 server/agent (and why should do that) or they don't know how you can writing Offensive codes for bypassing #avs or #EDRs or #bypassing other things ... you don't know about these things or a lot other things which you should learn them outside of university "by yourself".
you can learn these things from #infosec #communities (with read Articles or Learn Courses which shared Publicly or Privately by #SecurityResearchers and #Pentesters or #redteamers or #blueteamers) and you need at least 2-3 years experiences for learn these new things.
Some guys think if you know all tools in Kali linux then you can call yourself #Pentester or Red-teamer, which is not true "geniuses".
Penetration testing is not about Tools , its about background "concepts" of tools omfg "remember this". (its about logic behind tools)
Guess it's about time I do a #introduction
I go by ch33z_plz, I am a #RedTeamer/Penetration tester. I don't post much as I have little anxiety about it, but I will try to do more on here. Outside of InfoSec, I am interested in hobbies such as sculpting, skydiving, adventures with my dogs, getting tattooed, traveling, and of course eating all the #cheese 🧀