some little bit codes added to my Blue team code to detect some opcodes in injected bytes (especially for this DripLoader or something like this code)
this update version still needs some codes to be better but i working on this hard ;D , just for test some codes in Driploader.cpp was changed by me only for test ;)
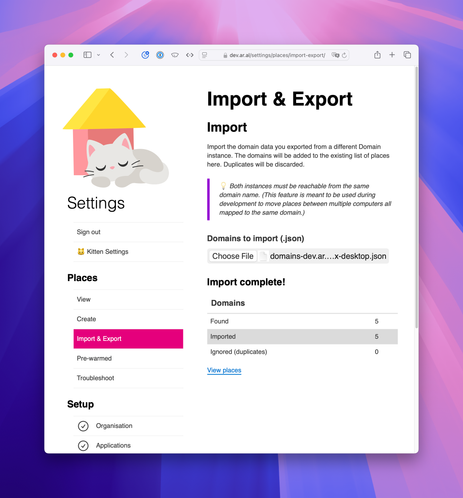
i Tested old Loader called "#DripLoader" , and this will bypass ETW events but my blue team tool not fully bypassed and code was detected...
background of this code is really nice and i working on this so maybe you want to see what happened in my test about this as #pentester or #Redteamer this will help you to better understanding ETW or other #eventbased #detections .
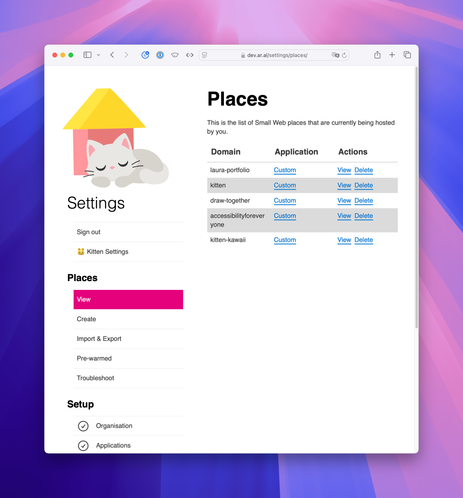
as #blueteamer you can see this with this method sometimes your tools will confuse very simple ;p in these pictures you can see startaddress via ETW was not Detected correctly.
Note: it does not mean that sartaddress is fake, i just want to say that startaddress 0x7ffca90... is not about shell code which started with bytes {0xb8 , 0x00 , 0x00 , 0xdd, 0xdd},its about jmp,Mov/BaseAddress/0xdddd0000 & you can find that bytes in C++ source code of driploader:
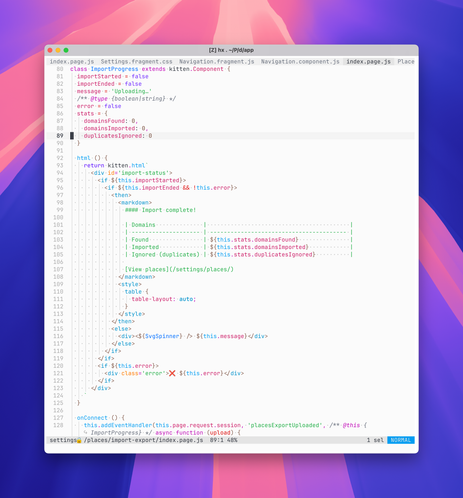
line 12 of DripLoader.cpp
unsigned char jmpSc[7] {0xB8,b[0],b[1],b[2],b[3],0xFF,0xE0};
worth to read =>
more detail about background of code: https://lnkd.in/ekpHUBsv
this code was added to my list long time ago => https://lnkd.in/eeStM9C
#blueteam #tools #redteam #pentesting #avs #edr #socanalyst #soc
#etw #threadinjection #threathunting #threatdetection
 💕
💕
 Mike Amundsen
Mike Amundsen