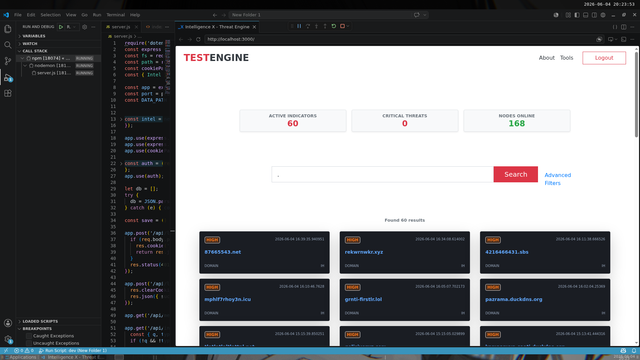
I'm a student and independent AI / Cyber Security Researcher Focusing on reverse engineering for the last 5 years and i wanted to share a quick threat intel project:
- I copied some IntelX UI components for the prototype.
- Integrated a part of USOM data—a national open-source feed—for testing.
Looking forward to connecting with the global #Infosec community here!
#ThreatIntel #CyberSecurity #PoC #BuildInPublic