@firstyear In the libkrimes README.md you write: "While RFC8009 does exist, it should be noted that no KDC we have tested with supports it in their latest versions (last tested June 2024)."
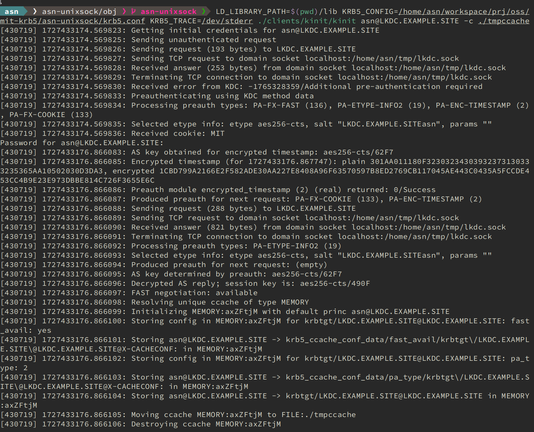
I wonder which KDC you have tested, because AES-SHA2 has been added in MIT Kerberos 1.15: The aes128-sha2 and aes256-sha2 encryption types are new in release 1.15.
See https://github.com/krb5/krb5/blob/master/doc/admin/conf_files/kdc_conf.rst#encryption-types
Sadly Windowser Server 2025 still doesn't support it yet.